The Retrospection of Cyberattack on the SWIFT Service Provider EastNets by Equation Group

1.Incident background
As the source of cyberspace attack activities, the cyber threat actors have different purposes and motivations, and their capabilities also have significant hierarchical differences. According to the motivation of the operation, the attack capability, and the control of resources, Antiy divides the cyber threat actors into seven levels, namely amateur hackers, black production organizations, cybercrime groups or hacker organizations, cyber terrorist organizations, general-capacity national/regional actors, high-level-capacity national/regional actors, and ultra-high-capacity national/regional actors (see Appendix I). Among them, ultra-high-capacity national/regional actors, or ultra-high-capacity cyber-threatening actors, have a strict scale system, a large supporting engineering system, and the control of systematic attack equipment and attack resources, which can carry out the most concealed and deadly cyber attacks. Antiy once called this kind of cyberattack as A2PT (the advanced APT).
The “Equation Group” is just such a typical ultra-high-capacity cyber-threatening actor. It was first publicly disclosed by Kaspersky in February 2015. Kaspersky claimed that it has been active for nearly 20 years and is probably one of the most sophisticated APT attack groups in existence[1]. Antiy has been continuously tracking the threat behavior of the “Equation Group” for many years since March 2015 and has published four analysis reports: A Trojan That Can Modify the Hard Disk Firmware: Exploring the Attack Components of the “Equation Group”[2], which analyzed some of its Trojan module components and the mechanism based on hard disk firmware persistence; Analysis of Encryption Techniques in Some Components of the “Equation Group”[3] revealed the encryption methods of its resources; From Equation to Equations: The Entire Platform Capability Analysis of the Advanced Malware of the “Equation Group”[4], revealed the full OS platform coverage capacity of its Trojan payload, and exclusively exposed the samples against Solaris and Linux; The Analysis of Equation Drug Platform of the “Equation Group”[5] formed a block puzzle of its atomized operation Trojan. Among these works, our biggest regret was that the analysis still remained in the perspective of malware analysis. We can only carry out the analysis work based on the limited extraction results from the scene where the attack target has been achieved, and combine samples associated with the threat intelligence extension line. From the published analysis results in the industry, both the activities of the “Equation Group”, and attacks of Stuxnet[6], Flame[7], and Duqu[8] from the ultra-high-capacity cyber threat actors, are based on the replay of principle analysis of the used vulnerabilities, the reverse analysis of the samples, and the affected mechanism of the samples. Although these tasks are complex and difficult, it cannot cover the defenders’ deficiencies in tactical and process perceptions of ultra-high-capacity cyber threat actors. This is because the ultra-high-capacity cyber threat actor represented by the “Equation Group” has a complete and rigorous operational framework and method system; it has a large-scale supporting engineering system and standard equipment portfolio, which can carry out strict organizational work; the pursuit of the concealment and back-tracking of the operation process makes the attack seem to be “non-trace ballistic”; it’s difficult to detect its breakthrough, existence, influence, and persistence until the safe exit of the network environment or the trajectory of the system, resulting in the defender’s little knowledge about the actual attack Techniques, Tactics and Processes (TTP) and the corresponding trajectories in the cyber operations, including research analysis, information collection, environmental shaping, early-time reconnaissance, entry breakthrough, lateral movement, persistence, and concealment confrontation, information acquisition, and long-term control. Therefore, it is impossible to grasp and interpret the information comprehensively from the perspective of the whole threat framework.
With the exposure of Snowden, there are more literature that can be analyzed for the relevant engineering systems and equipment systems of the ultra-high-capacity cyber threat actors. And the Shadow Broker’s disclosure revealed a batch of attack equipment. On the one hand, the breach of these exploits and malware payloads was quickly and widely used by other low-level cyber threat actors, resulting in information disasters (such as the outbreak of WannaCry); on the other hand, it has also become the invaluable research resource for security researchers to analyze the full range of attack activities of ultra-high-capacity cyber threat actors from a complete threat framework.
On April 14, 2017, the data exposed by the Shadow Broker contained a folder called SWIFT, which fully exposed the detailed information of two cyber attack operations by the “Equation Group” against SWIFT financial service providers and partners: “JEEPFLEA_MARKET” and “JEEPFLEA_POWDER”. Among them, operation “JEEPFLEA_MARKET” was launched between July 2012 and September 2013 against EastNets (the largest SWIFT Service Bureau in the Middle East), which has successfully stolen thousands of employee accounts, host information, login credentials and administrator accounts in Belgium, Jordan, Egypt and the United Arab Emirates; operation “JEEPFLEA_POWDER” that mainly targeted BCG (Business Computer Group,the partner of EastNets in Latin America and the Caribbean) did not succeed.
By combining years of analysis of the the “Equation Group” with the various information clues exposed in this folder, Antiy CERT restored the attack process of the “Equation Group” against the EastNets network. Through the replay, we can see that this is an APT event initiated by a ultra-high-capacity cyber threat actor, targeting financial infrastructure and attacking from a preset springboard in multiple regions around the world; it directly broke through the two-layer network with 0Day vulnerability with a persistent backdoor embedded; it obtained the internal network topology and login credentials to determine the next attack target; it used 0Day vulnerability of the “Eternal” series to break through the intranet Mgmt (management server), SAA service server and application server, and implanted the backdoor into the server system by multiple kernel-level (rootkit) implanting equipment; it was remotely controlled through a platform with complex instruction system and control function, and executed SQL scripts on the SAA service server to steal key data information of multiple target database servers.
The analysis team of Antiy strives to form the process replay with the thought of situation awareness, and conducts preliminary extraction and demolition of the attack activities of the ultra-high-capacity cyber threat actors with the interpretation in the perspective of threat framework, which would provide the reference on how to establish an effective defense system to the planners, constructors and operators of important information systems and key information infrastructure.
2.Assets of the target under attack
2.1 Introduction of SWIFT
SWIFT is short for Society for Worldwide Interbank Financial Telecommunications, which was formally established by 239 banks from 15 countries in the Americas and Europe in May 1973 and headquartered in Brussels, capital of Belgium. The organization operates a world-class financial messaging network where banks and other financial institutions exchange financial messages with peers through secure, standardized and trusted channels. In addition, SWIFT also sells software and services to financial institutions. By 2015, SWIFT’s services have covered more than 11,000 banks and securities institutions, market infrastructure and corporate customers in more than 200 countries and regions worldwide with 15 million daily messages.
2.2 Introduction of the SWIFT service provider under attack
The certified SWIFT Service Bureau (there are 74 in the world currently) provides customers with an efficient way to access the full SWIFT service, which is equivalent to the customer’s cloud provider. The target of the attack, EastNets, is the largest SWIFT Service Bureau in the Middle East.
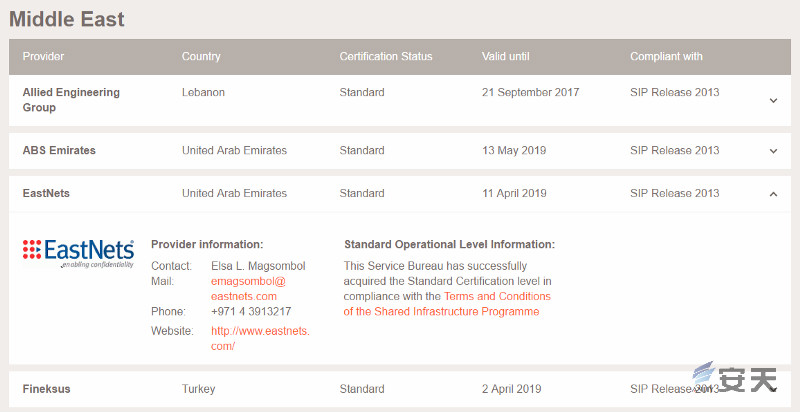
Figure 2-1 Introduction of EastNets organization
Headquartered in Dubai, EastNets is the world’s leading provider of compliance and payment solutions for financial services, offering a wide range of services related to SWIFT transactions, including compliance, customer understanding and anti-money laundering. Over the past 35 years, EastNets has leveraged its expertise to help clients combat financial crime, develop and implement standardized and personalized solutions, and provided risk management, monitoring, analysis, state-of-the-art advisory services and customer support. EastNets also focuses on end-to-end payment solutions that enable financial institutions to turn traditional payment challenges into opportunities and operate more efficiently and cost-effectively. More than 750 clients, including some of the largest international financial institutions, rely on EastNets solutions and professional services, and more than 270 enterprises and financial institutions rely on EastNets to provide outsourced SWIFT connectivity and compliance software solutions. EastNets has regional offices in major cities around the world and is supported by a broad network of global strategic partners[9].
According to the statistics of Treasury And Risk[10], 70% of the members who join SWIFT will choose SWIFT service providers to avoid the excessive investment caused by self-building SWIFT and the cost of subsequent operation and maintenance. SWIFT service providers are like the “cloud” of customers, which manage SWIFT transactions and information exchange between customers through Oracle database and SWIFT software. Because of the access to all of these bank transactions, many SWIFT service providers can also provide compliance, customer understanding and anti-money laundering services.
2.3 Profile of target assets under attack
By analyzing the attacks of the “Equation Group”, we can find that the EastNets network environment has a certain level and partition design from VPN access, area border to management servers, application servers and database servers according to different functional characteristics. It has made Port-based and IP-based access control policies and employed an enterprise-class firewall among each logical partition, and deployed mainstream brand security protection software on the server. Although this kind of network information system has a certain basic protection capability and defense depth, it is still compromised when facing the attack of super high-capacity cyber threat actors.
In this attack, the assets attacked by the EastNets network include VPN firewall devices, enterprise firewall devices, management servers, application servers, SWIFT service servers, terminal host information, login credentials, security protection software and application software, etc. Figure 2 -2 depicts the topology graph of the main assets profile under attack.
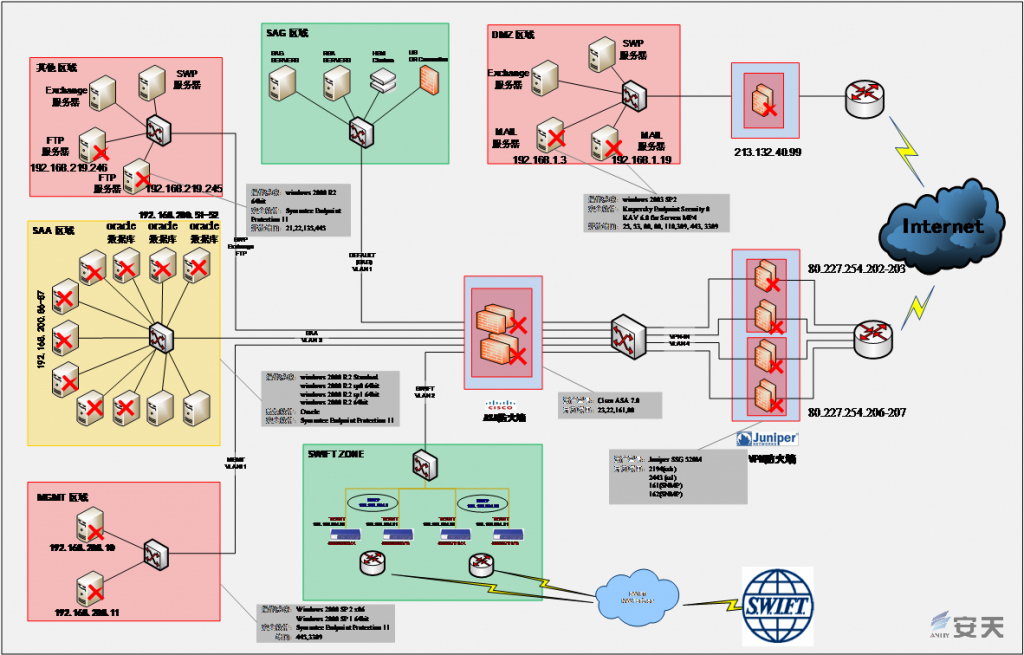
Figure 2‑2 Topology graph of the compromised asset profile
2.3.1 Network security device and network device information under attack
At least 10 network security devices and network devices in EastNets have been attacked or detected, and main brands are Cisco and Juniper. The names, software versions, opening ports and other information of relevant devices have been fully obtained by the “Equation Group” and leaked by “Shadow Brokers”. The details are shown in Table 2-1.
Table 2-1 Details of enterprise firewall devices under attack
| Name | Equipment Model | Version Information | Type | Opening Ports | Name of Attack Equipment | Compromised Vulnerability Number |
| ENSBDVPNSW1 | Netscreen | Unknown | Firewall | 22(ssh),2443 (ssl),161、162(snmp) | Unknown equipment A | CVE-2015-7755 |
| ENSBDVPN1 | Juniper SSG 520M | Unknown | Firewall(VPN) | 2194(ssh),2443 (ssl),161、162(snmp) | Unknown equipment A | CVE-2015-7755 |
| ENSBDVPN2 | Juniper SSG 520M | Unknown | Firewall(VPN) | 2194(ssh),2443 (ssl),161、162(snmp) | Unknown equipment A | CVE-2015-7755 |
| ENSBDVPN5 | Juniper SSG 520M | Unknown | Firewall(VPN) | 2194(ssh),2443 (ssl),161、162(snmp) | Unknown equipment A | CVE-2015-7755 |
| ENSBDVPN6 | Juniper SSG 520M | Unknown | Firewall(VPN) | 2194(ssh),2443 (ssl),161、162(snmp) | Unknown equipment A | CVE-2015-7755 |
| ENSBDASA1 | Cisco | ASA Version 7.0 | Firewall | 23(telnet),22(ssh),161(snmp),80(http) | EPICBANANA EXTRABACON | CVE-2016-6367 CVE-2016-6366 |
| ENSBDPIX3 | Cisco | PIX Version 6.3 | Firewall | 80(http),161、162(snmp),23(telnet),69(tftp),22(ssh) | EPICBANANA EXTRABACON | CVE-2016-6367 CVE-2016-6366 |
| ENSBUSPIX | Cisco | PIX Version 8.0 | Firewall | 80(http),161、162(snmp),23(telnet),69(tftp),22(ssh) | EPICBANANA EXTRABACON | CVE-2016-6367 CVE-2016-6366 |
| ENSBUSPIX2 | Cisco | PIX Version 8.0 | Firewall | 80(http),161、162(snmp),23(telnet),69(tftp),22(ssh) | EPICBANANA EXTRABACON | CVE-2016-6367 CVE-2016-6366 |
| ENSBDRTR1 | Unknown | version 12.4 | Voice gateway | 80(http),161、162(snmp) | ||
| ENSBPSW1 | Unknown | version 12.2 | Switch | 80(http),23(telnet) | ||
| ENSBPSW2 | Unknown | version 12.2 | Switch | 80(http),23(telnet) |
2.3.2 Management server information under attack
There are two management servers under attack, and the intranet IP addresses are 192.168.206.110 (192.168.208.10 / 10.255.10.10) and 192.168.206.111 (192.168.208.11 / 10.255.10.11). The host name, MAC address, opening ports, security protection software, version, administrator user name and password information of relevant servers have been fully obtained by the “Equation Group” and leaked by “Shadow Brokers”. Both servers are Windows Server 2008, with ports 445 and 3389 open, one with Symantec endpoint protection software and the other without. The details are shown in Table 2-2.
Table 2-2 Details of management servers under attack

2.3.3 Application server information under attack
There are 4 application servers under attack, including mail servers, FTP server and so on. The host name, MAC address, opening ports, security protection software, version, administrator user name and password information of relevant servers have been fully obtained by the “Equation Group” and leaked by “Shadow Brokers”. Two FTP servers are Windows Server 2008 with 21 port open. One of them also opens ports 22, 135, and 446. Both servers are equipped with Symantec endpoint protection software. The other two mail servers are Windows Server 2003. The mail systems are built by Exchange Server and protected by Kaspersky endpoint protection software. Both servers have DNS service ports open, one provides SMTP and POP3 services, and the other provides Webmail services based on the HTTPS protocol via OWA (Outlook Web Access).
The details are shown in Table 2-3.
Table 2-3 Details of application servers under attack

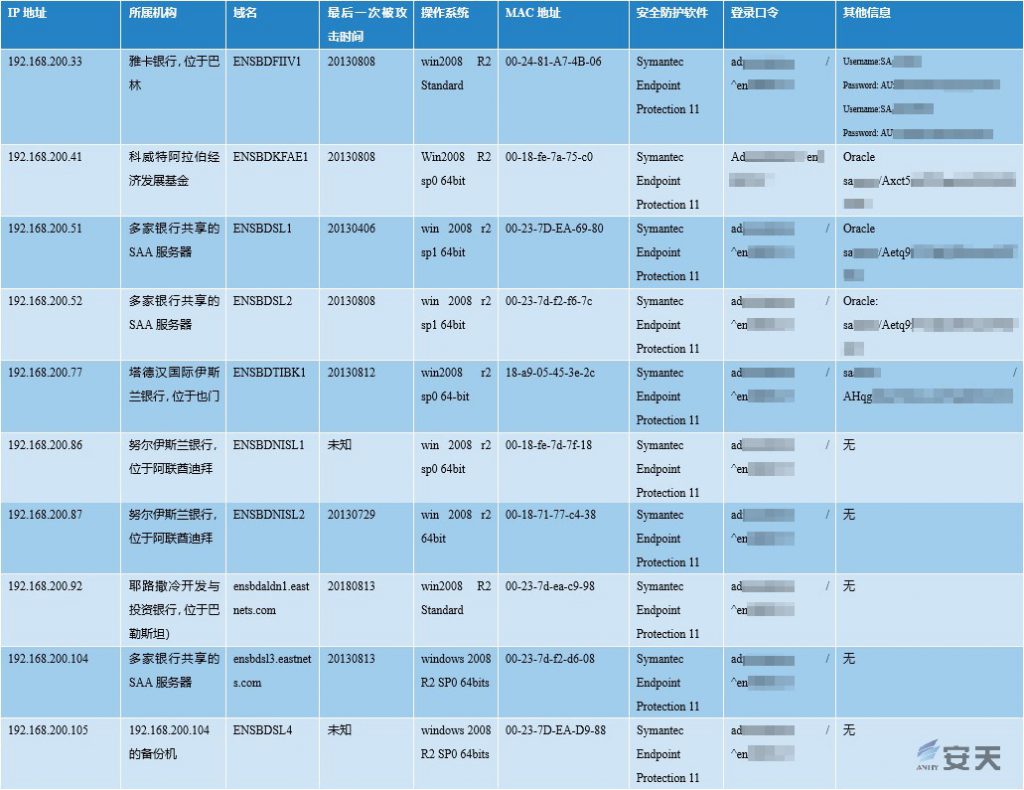
2.3.4 SWIFT business server information under attack
There are ten SAA (SWIFT Alliance Access) servers under attack, of which six are owned by five Middle Eastern banks, three are SAA servers shared by multiple banks, and one is a backup server sharing SAA. These server operating systems are Windows Server 2008, installed with Symantec’s endpoint protection software and configured with the same administrator password. Nine of the ten servers were compromised by the “Equation Group”, and seven of them had related attack log records. The host name, MAC address, opening ports, security protection software, version, host administrator user name and password information of the ten servers, as well as the administrative username and password information of the Oracle database running on the three SAA servers are leaked by “Shadow Brokers” . Give way. The details are shown in Table 2-4.
Table 2-4 Details of SAA servers under attack
2.3.5 Stolen information asset information
The stolen information assets mainly include login credentials of network devices and network security devices, and business data of several banking institutions (such as account name, account status, password) in the SAA business server. According to the profile information used for analyzing network devices and the network security devices, no less than 300 login credentials are stolen. Table 2-5 shows some of the stolen information after masking. According to this information, it can be judged that the purpose of the attack of the “Equation Group” is to obtain some of its interested accounts and passwords, and to further obtain its capital status, transaction information, capital flow trajectories and so on.
Table 2-5 Partial information of stolen information asset
| User name | Password | User name | Password |
| msaeed | nF3dKrrk************************ | h*** | y52jzNa********************* |
| adesear | nIVbOVr************************** | j** | A1DtwtZ********************* |
| juy | nGB6Dq************************** | m****** | RqCPQY********************* |
| kbaluyot | nMSQP4************************** | a****** | XvqGprsO********************* |
| adesear | 0TjLvUu************************** | A********* | sLLc3lXk********************* |
| juy | dT36Q1n************************** | A********* | MrItc2baN********************* |
| kbaluyot | 9b9kpb/w************************** | A***** | zWmfh2+s********************* |
| adesear | +YdYUF************************** | S******** | AuaXPsV********************* |
| arousan | Osqe9vI************************** | S******** | GCZKD2q********************* |
| juy | 4W7Mv************************** | S******** | F87E/Du2********************* |
| kbaluyot | IsKcgG************************** | S******** | kEXo5+/********************* |
| msaeed | bVe7xU************************** | S******** | RbXNRH********************* |
| msalameh | 0HrX+************************** | S******** | fELIIrMf********************* |
| relkheir | 2Uwcti************************** | S******** | sjEWUX********************* |
| mserhan | nBJrKh************************** | S******** | iwE8Z********************* |
| rmahmoud | nGZ/Nk************************** | S******** | Cs7DN********************* |
| mzaidi | nHY/Izr************************** | S******* | U4HXR********************* |
| ARousan | qqlIj6g************************** | S******* | 0rAzjVg********************* |
| EMagsombol | EMjYQ************************** | S******* | A2QlRqt********************* |
| KShahzad | fxSoe9z************************** | S******* | 6mztaDz********************* |
| LAbuezz | 4hcS1T1************************** | a****** | Rw4kEbt********************* |
| PPU | x8pz0PS************************** | a****** | cpmVyDS********************* |
| SJaber | RHNlQn************************** | a****** | e5ahpYss********************* |
| SQasim | UKRAu************************** | j** | sSf6pikE********************* |
| adesear | ncmSPF************************** | t*********** | PJx0Q********************* |
| aibrahim | v/+gad1************************** | a**** | v7r5W********************* |
| ajaber | iscut//ZN************************** | a****** | AyUo********************* |
| asalameh | fdH9+Ko************************** | k******* | veUj********************* |
| bics-test | cNdhQ************************** | m***** | HrG. ********************* |
| dgradinarov | vvDEin************************** | m****** | omTb********************* |
| emagsombol | 1Jg7Zd************************** | r******* | cmhH********************* |
| finmex | c7q/ST************************** | j****** | ZT2jq********************* |
| finmex_mgmt | bV7Hh************************** | a**** | nHr9J********************* |
| gruiz | 2VU35r************************** | s****** | Aetq9f********************* |
| hkharbat | jkZsfUM************************** | s****** | AF1T********************* |
| juy | 0a7W6+************************** | d******* | dxbr********************* |
| juy_dxb | gj2vh2************************** | d******* | dxbr********************* |
3.The attack equipment used in the incident
The attack equipment used by the “Equation Group” to attack EastNets covers multiple devices and endpoint systems in EastNets’ informational scenarios, including VPN firewall devices at the network boundaries, enterprise-class firewall devices, management servers, and SAA servers that support SWIFT services. These attack equipment can be roughly divided into three categories: vulnerability exploitation tools and attack platforms, persistence tools and control/backdoor malicious code, and full set of attack equipment has the attack capability covering the whole platform and system. [4]
3.1 Vulnerability exploitation tools and attack platforms
The related vulnerability attack equipment is mainly aimed at network security devices and various types of endpoint systems, such as network devices and firewalls. Its main function is to break through the boundary, move horizontally and obtain the authority of the target system, so as to open channels for subsequent implant persistence and control load. The typical vulnerability attack equipment EPICBANANA, EXTRABACON and an unknown device are for the firewall. In this attack, the “Equation Group” uses advanced FuzzBunch vulnerability exploit platform[11] to work on Windows systems (it contains at least 17 exploit plugins, 5 of which may be used for this action). See the table below for details:
Table 3‑1 The list of vulnerability exploitation tools used to attack EastNets
| Name of Attack Equipment | Vulnerability Number | Target Equipment And its Functions |
| Unknown device A | CVE-2015-7755 | Unknown device A is a vulnerability exploitation device for Juniper ScreenOS (the operating system used by Juniper SSG and NetScreen firewall products). There is an identity bypass vulnerability when logging into the Juniper firewall through SSH and Telnet. |
| EPICBANANA | CVE-2016-6367 | EPICBANANA is a vulnerability exploitation device for the command-line interface (CLI) parser in Cisco ASA and PIX devices; |
| EXTRABACON | CVE-2016-6366 | EXTRABACON is an SNMP service (port 161, 162) vulnerability attack equipment for Cisco ASA devices; |
| ENTERNALCHAMPION | CVE-2017-0146 | ENTERNALCHAMPION is the vulnerability attack equipmentthe “Eternal” series, aiming at Windows Server 2008 SP1 x86. It exploits Windows SMBv1 remote code execution vulnerability; |
| ETERNALSYNERGY | CVE-2017-0146 | ETERNALSYNERGY is the vulnerability attack equipmentthe “Eternal” series, aiming at Windows 8, etc. It exploits Windows SMBv1 remote code execution vulnerability; |
| ETERNALBLUE | CVE-2017-0143 CVE-2017-0144 CVE-2017-0145 CVE-2017-0146 CVE-2017-0148 | ETERNALBLUE is the vulnerability attack equipmentthe “Eternal” series, aiming at Windows 7/8/XP. It exploits Windows SMBv1 remote code execution vulnerability; |
| ETERNALROMANCE | CVE-2017-0143 | ETERNALROMANCE is the vulnerability attack equipmentthe “Eternal” series, aiming at Windows XP, Vista 7, Windows Server 2003/2008/2008 R2, etc.. It exploits the SMBv1 remote code execution vulnerability of Windows full platform; |
| EXPLODINGCAN | CVE-2017-7269 | EXPLODINGCAN is an attack equipment that exploits the IIS6.0 webDAV vulnerability. |
At the time of this attack, the vulnerabilities used above were all undisclosed. The total number of vulnerabilities used in this attack exceeds that of the “Stuxnet” attack (5 Windows 0day and 1 Siemens 0day vulnerabilities were used in the stuxnet attack), reflecting the high-capacity cyber threat actor’s sufficient attack resource reserve. The “Eternal” series of exploit tools are loaded on the FuzzBunch attack platform. FuzzBunch is a powerful attack platform similar to MetaSploit that covers a large number of exploits and payloads. It operates in a line command mode, which mainly includes touch tool set, exploit tool set, implant and configuration update tools and payload module. The touch module is used to obtain the the fingerprint information of the host system and related services, the open port that can be attacked, and to determine whether there is a specified vulnerability in the target; There are at least 17 exploit modules in the vulnerability exploit tool, two of which are known as Specials vulnerability, namely the Eternal Blue and Eternal Champion, two heavyweight vulnerabilities – this logo may be used to ensure that the use of relevant vulnerabilities is highly prudent. There are two modules in the implant tool, which are used to transfer and load the attack payload to the attacked host, and to deliver and update the relevant configuration files. The function payload plugins set is mainly used to install the backdoor, load the DLL, enumerate the process, add and delete the registry entry, RPC service, etc., to the target after the vulnerability module attack succeeds. It establishes a remote control operation mechanism on the host side, which are in line with the judgment of Antiy on the Trojan “frame-design”, “modularization of components” and “atomization of operations” in previous reports. The module structure of the FuzzBunch platform is shown in Figure 3-1.
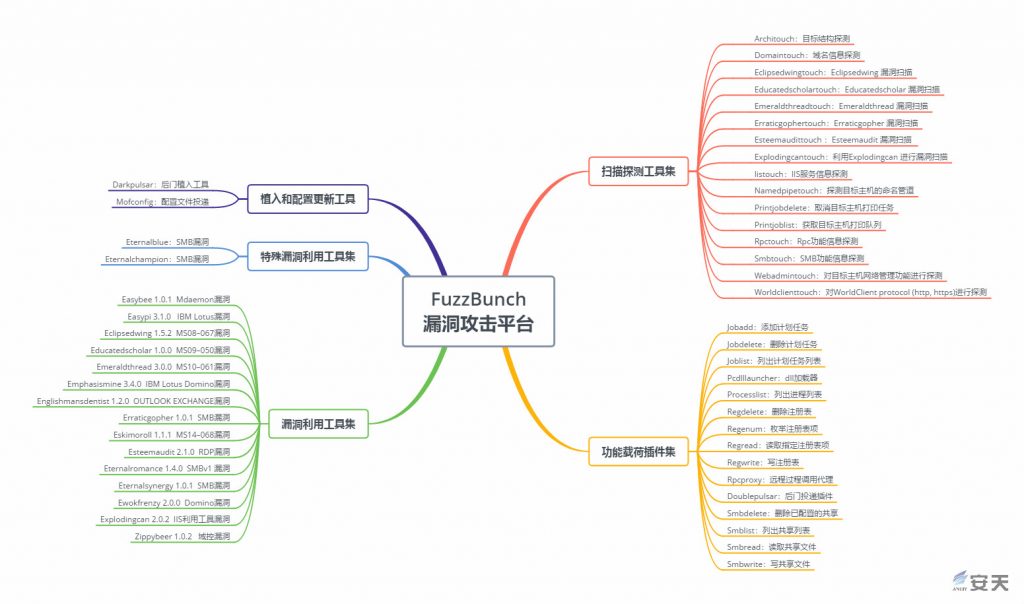
Figure 3‑1 The structural disassembly of FuzzBunch vulnerability attack platform
The vulnerability attack equipment used in this incident has been combed and analyzed by Antiy in the analysis report “Antiy’s manual on systematically responding to NSA cyber munitions”.[11] And Antiy mapped the exploit diagram, as shown in Figure 3-2.
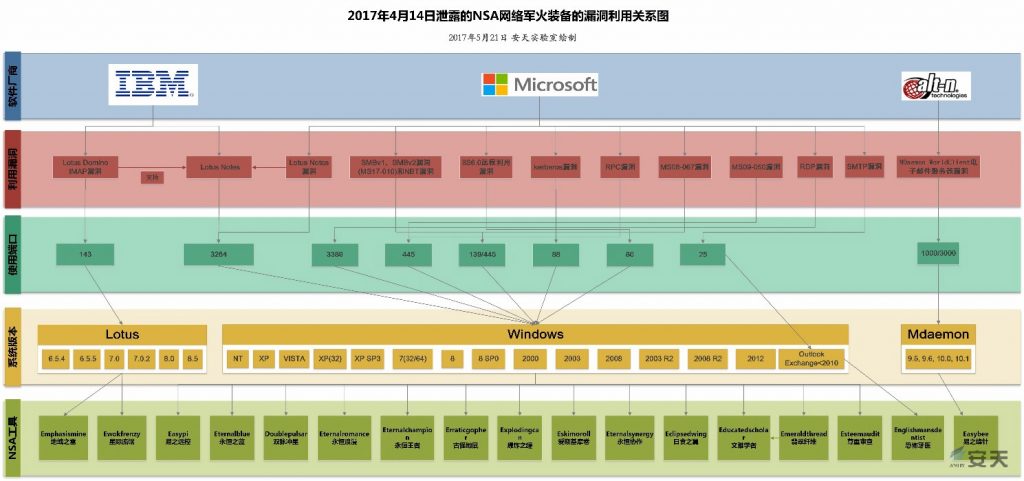
Figure 3‑2 Leaked exploit diagrams of NSA cyber munitions
3.2 Persistence / implant attack equipment
The super cyber threat actor attaches great importance to the ability to form a persistence in the target scenario, and has developed a large number of equipment to achieve persistence. Persistence attack equipment is usually used after breaking the target, mainly for BIOS/UEFI, firmware, boot sector, peripherals, etc., and it is difficult to find and deal with the deep loading point, or form a repeatedly implanted window of opportunity. Ensure sustainability capability in advanced persistent threat (APT) activities. Through the loading opportunity provided by persistence, the attacker can maintain the initial connection and initial control with the target system, Through the loading opportunities provided by persistence, the attacker can maintain initial connection and initial control with the target system, and further deliver complex attack payloads to achieve complete control and management of the target. The following persistence equipment was used in this attack:
Table 3‑2 Persistence/implantation attack equipment used to attack EastNets
| Names | Targeted devices and features |
| FEEDTROUGH | Persistent attack equipment for Juniper NetScreen firewalls devices |
| JETPLOW SCREAMINGPLOW | Persistent attack equipment against Cisco ASA and PIX devices |
| DoublePulsar Darkpulsar | An attack device that targets the kernel level (Rootkit) implantation of Windows system |
FEEDTROUGH[12] is an attack device for firmware layer persistence for firewalls such as Juniper and NetScreen. It can implant payload into the system when the firewall starts. This technology is exactly the same as the attack organization’s persistence idea of hard disk firmware.[2] It is a lower-level persistence technology that is difficult to detect and discover.
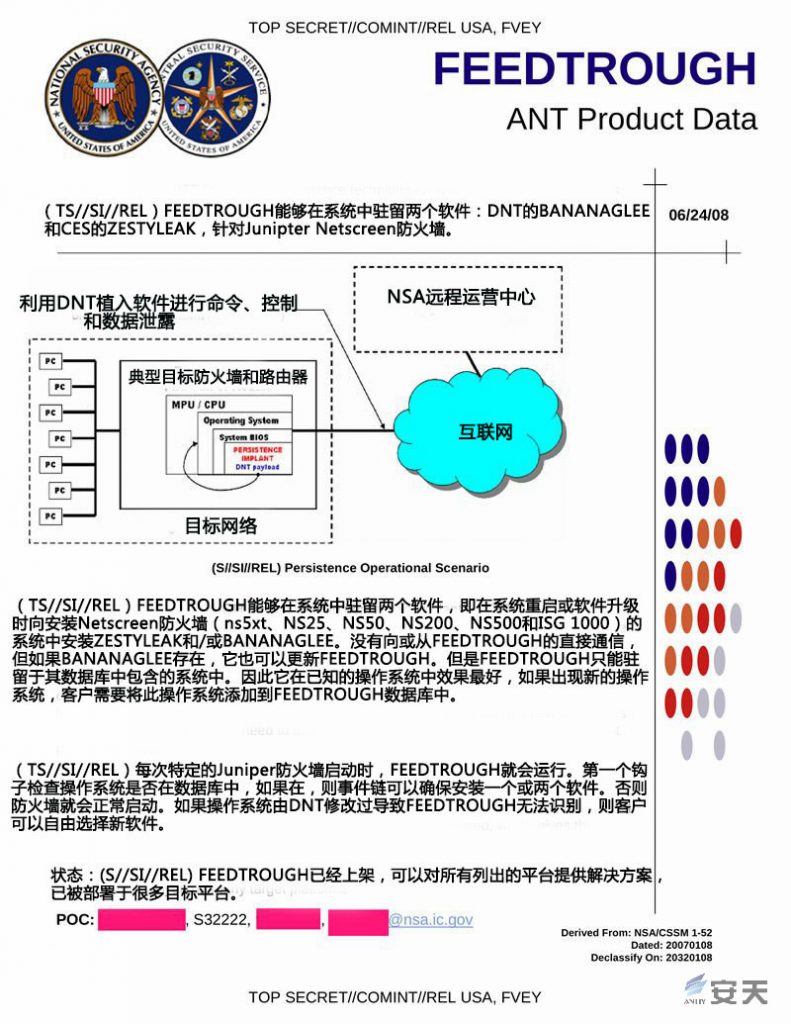
Figure 3‑3 ANT-FEEDTROUGH attack equipment
According to the analysis of Snowden’s exposure information, NSA’s subordinate department ANT (full name “advanced network technology” or “intrusion network technology” department) has FEEDTHROUGH’s persistent equipment, ANT has a complete set of persistent equipment, based on comprehensive coverage Endpoint systems, peripherals and interfaces, wireless networks and GSM cellular networks, mainstream network devices and network security devices, etc., enable delivery, implantation and persistence in a variety of information scenarios. In the early days, Antian had combed the attack equipment of ANT and formed the equipment system diagram of ANT, as shown in Figure 3-4.
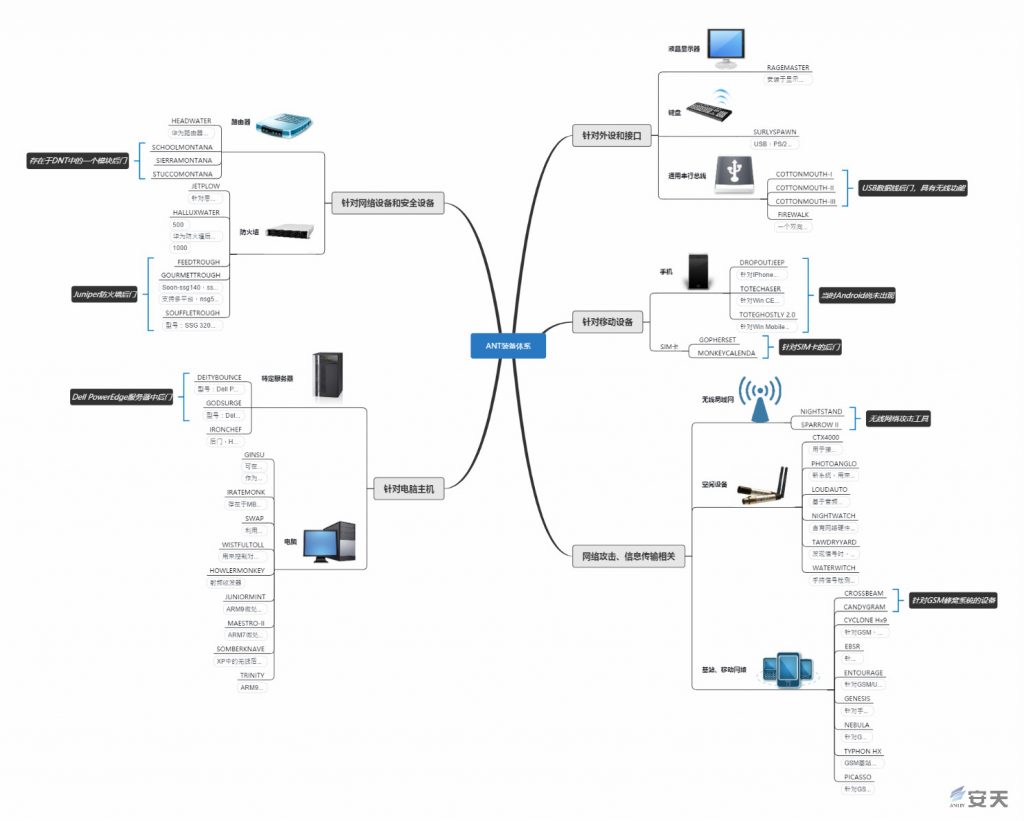
Figure 3‑4 ANT equipment system
3.3 Control / backdoor class malicious code
This type of attack equipment is the payload that is ultimately implanted into the target system during the attack and is used for persistence or non-persistence control of the target system. The attack equipment used by the attackers in this operation is shown in table 3-3. The first 7 items are for network security devices and network devices, and the last one is for Windows host systems. Unlike the persistent tools that seek to create hidden permanent access points, the control/post-class malicious code of the “Equation Group” emphasizes memory atomization module loading operations, the file does not land, minimizing the possibility of being discovered and extracted. The combination with the persistence tools is characterized by “hidden under the deep earth (firmware and other deep layer unknown), moving over the high sky(memory).
Table 3‑3 The control/backdoor attack equipment used to attack EastNets
| Names | Targeted devices and features |
| ZESTYLEAK | Control/backdoor attack equipment for Juniper firewall |
| BARGLEE | Control/backdoor attack equipment for Juniper NetScreen firewall |
| BANANAGLEE | The aim of memory non-persistent implants and a collection of non-persistent control tools (residing only in memory, failing after reboot) for Cisco ASA and PIX devices is designed to support nearly 20 functional modules after obtaining firewall privileges. And they can complete specific tasks such as “traffic redirection”, “traffic capture”, and “packet injection” and only reside in memory after successful implantation, enabling hidden operations that do not fall to the ground |
| SCREAMINGPLOW | A collection of non-persistence control tools for embedding Cisco ASA and PIX Series devices (residing only in memory and failing after reboot) to enable control of devices after obtaining firewall privileges |
| NOPEN | Backdoor attack kit for Linux systems |
| PITCHIMPAIR | UNIX backdoor attack equipment with redirection |
| INCISION | Backdoor attack equipment with rootkit and redirection |
| DanderSpritz | Full-featured remote control platform developed by the attacker |
DanderSpritz is the most typical control platform, which has a modular attack platform with strict operation process and rich evading means. Antiy has conducted a comprehensive analysis in the article “The Analysis of the ‘Equation Group’ EQUATION DRUG Platform “. DanderSpritz has an interfaced remote control platform with complex command system and control functions, which is obviously different from the traditional RAT program. Once it is implanted into the target system, it will collect all kinds of security configuration information of the system and prompt the attacker which configuration or information may cause itself to be discovered or detected.Its payload has various connection modes, among which the “Trigger” mode is an active connection mode that neither listens to the port nor sends out the connection. Instead, it listens to traffic and waits for the attacker’s activation packet, which makes the deployment of the console change. Flexible and difficult to be banned.
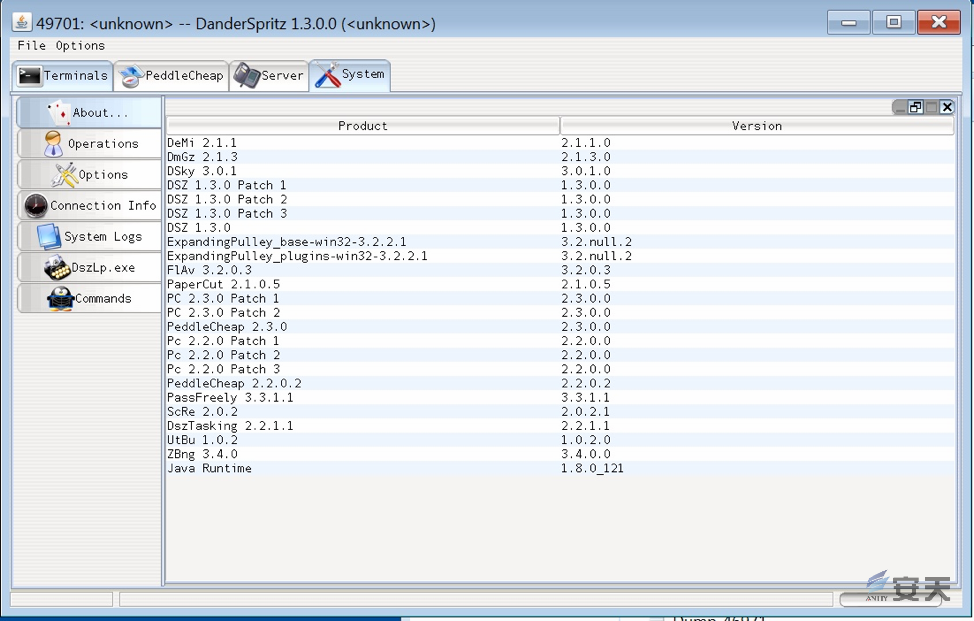
Figure3‑5 DanderSpritz remote control equipment interface
DanderSpritz has a modular architecture, a wealth of standardized attack tools and plugins, and is a representative of the “Equation Group” cyber weapons. In the previous analysis report, Antiy combed the other Trojan module plug-ins of the “Equation Group”, sorted out the combinations that these function plugins might form during the attack process, and mapped the “Equation Group” host operation module building block diagram.The diagram preliminarily shows a modular assembly of the host intelligence operations in accordance with the “atomic” split, as shown in Figure 3-6:
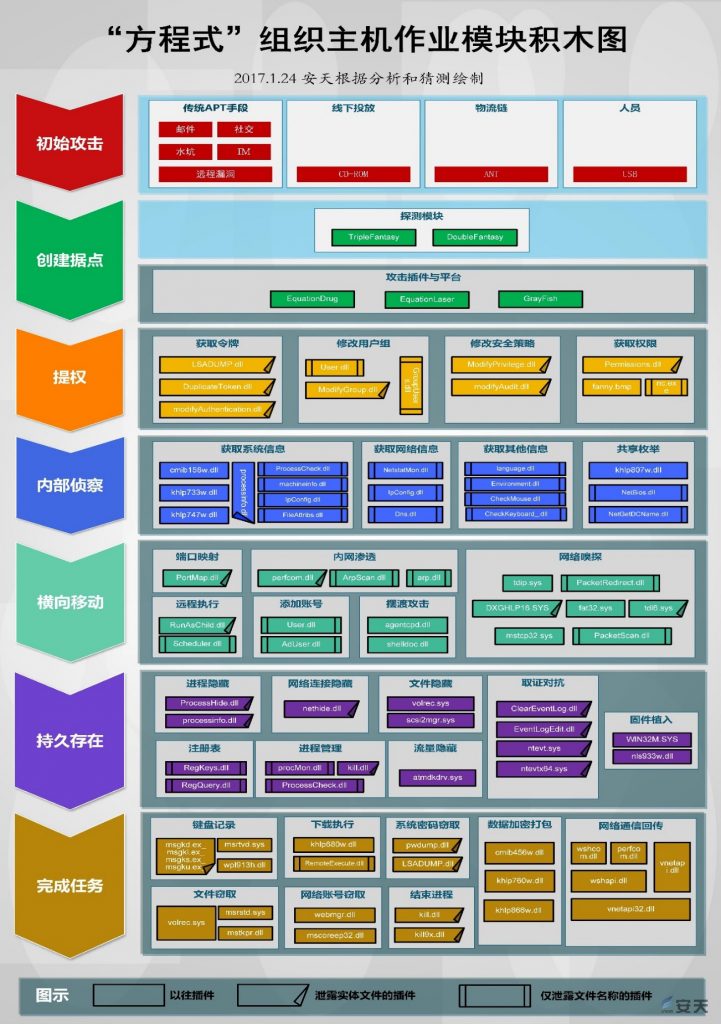
Figure 3‑6 The “Equation Group”building block diagram of host operation module
fine-grained functional instructions. For example, the “DoubleFantasy” weapon in the stronghold creation stage, has a branch instruction with clear division of labor (as shown in the figure below). The coordination of different commands can complete a series of operational actions.
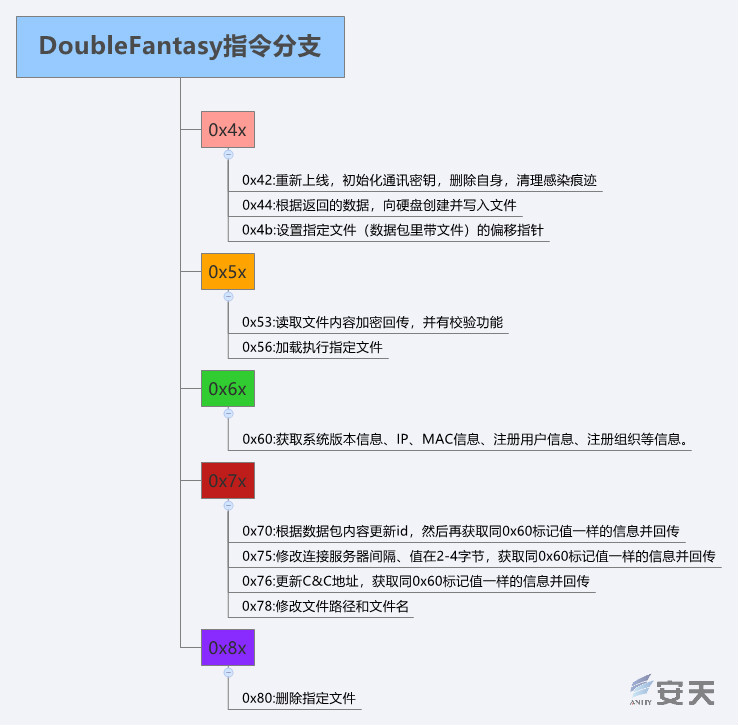
Figure 3‑7 DoubleFantasy Instruction branch
4 .Attack process reanalyze
From July 2012 to September 2013, the “Equation Group” launched six cyber attacks on EastNets using midpoints IP from a number of different countries and regions. The attacker cooperated with six different intrusion paths, using multiple sets of attack equipment including the “Eternal” series for different systems and devices, and finally captured 4 VPN firewall devices, 2 sets enterprise-class firewall, 2 management servers, and 9 SAA servers and FTP servers running multinational financial institution business systems in the EastNets network and mail servers located in the DMZ area.
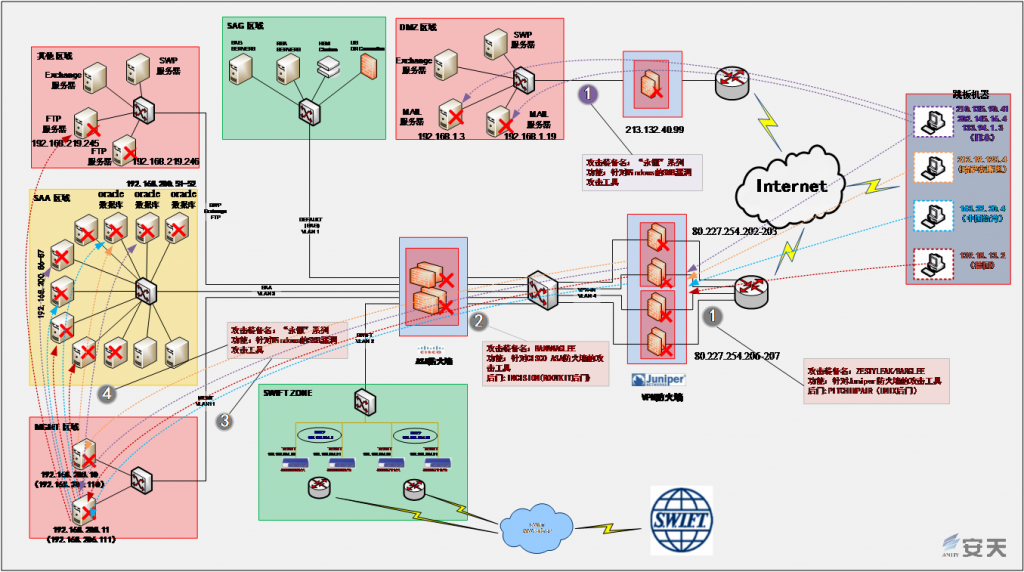
Figure 4-1 Re-analysis of the overall attack process of the “Equation Group”on the EastNets network
4.1 General attack process
From the general attack situation, the attacker used multiple 0Day vulnerabilities to break through multiple Juniper SSGs and CISCO firewalls through midpoints machines from multiple regions around the world, then implanted a persistence backdoor,and use 0Day vulnerabilities of the “Eternal” series to control subsequent intranet application servers, Mgmt Devices (admin servers) and SAA servers.In addition to breaking through the firewall, the attacker also broke through the mail server on the external network, scanned and collected information (such as security protection software and application software installation) on the external mail server and terminals in the same network segment. In the part of the attack process, although there are some failed operations such as failure to implant the persistence module into the terminal, through the multiple cooperation of multiple intrusion paths, the “Equation Group” finally completed the theft of bank institution data in many regions of the EastNets network.
Attack midpoints:
The Internet attack midpoints used in this attack is a commercial Unix, FreeBSD or Linux server host that is implanted in the back door of PITCHIMPAIR, most of which come from universities and research institutions all over the world. The operation of these nodes depends more on the robustness of the system itself, and the self-operation and maintenance of personnel in universities and research institutions, rather than being in the high-frequency confrontation of the Windows environment, this has driven the continuous improvement of the protection capabilities of commercial security products. For ultra-high-capacity cyber threat actors, this node outside the perception of commercial security capabilities has become an ideal target for establishing a persistent midpoints. At the same time, because these servers are located in universities and research institutions, they are not simply equipped with midpoints value, and they themselves are directly related to direct intelligence acquisition activities at different points in time. These nodes are used in different ways in different forms and task roles. In November 2016, “Shadow Brokers”published a list of servers that were invaded. The date of the list shows that the server nodes of the education, research, and operators in 49 countries in the Asia-Pacific region were attacked between 2000 and 2010. Affected countries include China, Japan, South Korea, Spain, Germany, and India. As shown in Figure 4-2, in related news, it is also mentioned that the relevant servers may be Linux, FreeBSD and Solaris. This is a very good mutual proof of the midpoints information used by the “Equation Group” to attack EastNets.
Table 4-1 The “Equation Group” attack midpoints machine used by EastNets network
| Attack time | Midpoints machine | Affiliation institution | Geographic location |
| 2012-07-02 19:10:51 UTC | ns.itte.kz(212.19.128.4) | RDT ALMATY TELECOM(RDT) | Kazakhstan |
| 2012-11-07 05:15:23 UTC | sunblade.kouku-dai.ac.jp(202.145.16.4) | Japan Aviation University | Japan |
| 2013-05-14 12:35:13 UTC | cis.cc.kurume-it.ac.jp(133.94.1.3) | Kurume Institute of Technology | Japan |
| 2013-06-05 17:55:19 UTC | euclid.csie.cnu.edu.tw(163.22.20.4) | Chia Nan University of Pharmacy & Science | Chinese Taipei |
| 2013-08-29 02:44:00 UTC | cnt1.din.or.jp(210.135.90.41) | Japan Dolphin International Company | Japan |
| 2013-09-04 15:57:40 UTC | isun02.informatik.uni-leipzig.de(139.18.13.2) | Universität Leipzig | Germany |

Figure 4-2: Invasion Visualization replay of global Internet nodes between 2000 and 2010 by the “Equation Group”
The general attack process is as follows:
Step 1: Select 6 compromised servers from Japan, Germany, Kazakhstan, and Chinese Taipei as a midpoint to attack the 4 Juniper VPN firewalls on the EastNets network using the Juniper ScreenOS Software Identity Vulnerability (CVE-2015-7755). After the attack is successful, the FEEDTROUGH persistent attack equipment is implanted into the firewall to the target system. Finally, FEEDTHROUGH is used to embed ZESTYLEAK and BARGLEE backdoor attack equipment into the firewall to achieve complete control of the firewall. In 2 of the 6 attacks, the vulnerability of the “Eternal” series attack equipment were used directly. In addition, it attacked the mail server located in the DMZ area and scanned the intranet.
Step 2: Attack 2 Cisco Enterprise Firewalls with EPICBANANA or EXTRABACON vulnerability attack equipment. After the attack is successful, JETPLOW or SCREAMINGPLOW is implanted into the target system. Finally, BANANAGLEE is implanted into the firewall system through JETPLOW or SCREAMINGPLOW to achieve complete control of the firewall.
Step 3: Use the 0Day vulnerability of the “Eternal” series to attack two management servers. After the attack is successful, implant DoublePulsar or Darkpulsar into the server system. Finally, the backdoor load (DLL) generated by the DanderSpritz platform is implanted into the server system through DoublePulsar or Darkpulsar for remote control.
Step 4: Take the 2 management servers as a midpoints and use vulnerability of the “Eternal” series to obtain control of the 9 SAA service servers on the back end. The vulnerability of the “Eternal” series used include ETERNALROMANCE, ENTERNALCHAMPION, ETERNALSYNERGY and ETERNALBLUE. Finally, the SQL scripts initial_oracle_exploit.sql and swift_msg_queries_all.sql are executed on the SAA server to dump the business data (account name, account status, password, etc.) of a plurality of banking institutions stored in the local Oracle database. It also attacks the FTP server in other areas through the management server.
4.2 Visualization replay
According to the above summary analysis, the replay demonstration of the attack action by the Antiy Situation Awareness Platform visualization component is shown in Figure 4-3.
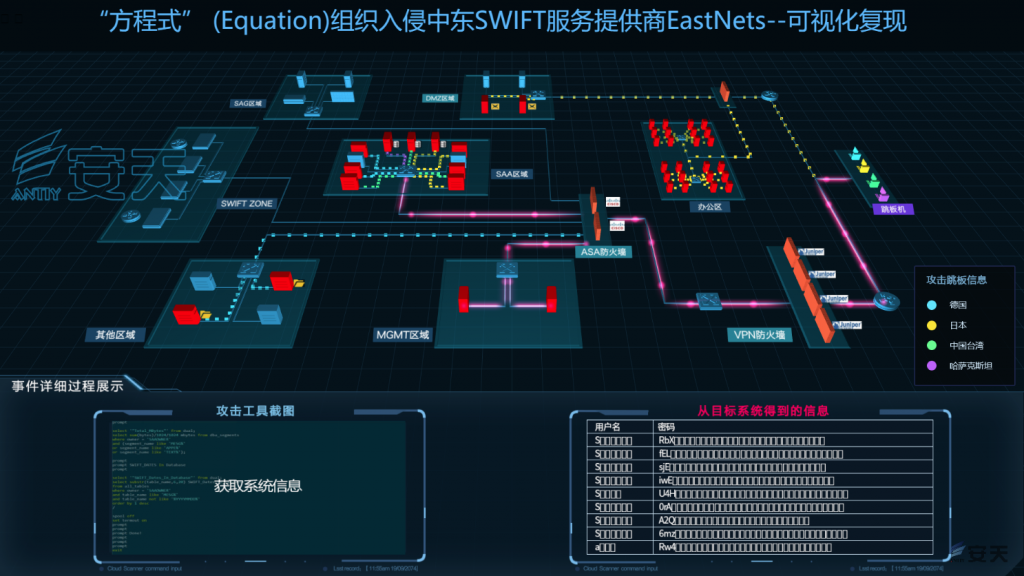
Figure 4-3 Replay demonstration of the attack by the Antiy Situation Awareness Platform visualization component
5.Analysis of mapping between the cyber threat framework and this incident
The ultra-high-capacity cyber threat actors represented by the “Equation Group” have the characteristics of a large attack support engineering system, equipment system and large-scale operation team, and successfully carry out highly complex attacks under the support of these resources. If the analysis of similar attack organizations stays in a single point of 0day vulnerability, malicious code, etc., it will be not helpful to comprehensively analyze the whole process, and it is difficult to effectively guide the defense work. In order to cope with the attack activities of high-capacity cyber threat actors, security personnel need to have a systematic and framework threat analysis model to conduct deeper and systematic analysis of their behaviors, understand threats, and achieve more effective defense. Current similar analytical models include Lockheed Martin’s Kill Chain and MITRE’s ATT&CK.
Kill Chain was proposed by Lockheed Martin in 2011. It defines the seven stages that an attacker must complete in order to achieve the goal. He believes that the defender can break the chain at any stage and can prevent the intruder from attacking. Kill Chain models network attacks to help guide the identification and defense of cyber attacks. However, the overall granularity is coarse and comprehensive, and the corresponding countermeasures lack detailed support. In order to solve the above problems, MITRE proposed the ATT&CK model based on Kill Chain, namely the tactical, technical and general knowledge base. It divides what can happen during the entire lifecycle of the intrusion into 12 phases, namely initial access, execution, privilege escalation, defensive evasion, credential access, discovery, lateral movement, collection, command and control, oozing and impact, each The stages are subdivided into specific attack techniques. ATT&CK provides a detailed description of each technology, methods for monitoring, and mitigation measures to help security personnel better understand the risks and preventive work of the network. However, ATT&CK focuses on specific attack techniques and is weak in terms of hierarchy and classification of intrusions.
The NSA and CSS referenced various existing frameworks and released the NSA/CSS Technical Cyber Threat Framework (hereinafter referred to as the“Threat Framework”) Version 1 in March 2018. The framework is a general-purpose technical dictionary developed in close collaboration with cyberspace activities based on the National Intelligence Director (DNI) Cyberspace Threat Framework. The NSA shares this dictionary throughout the intelligence system, enabling support for intelligence sharing, product development, and operational planning, and fostering closer collaboration between agencies in the intelligence system.
As the network threat escalates, the NSA and CSS adjust and extend the “Threat Framework” Version 1, and reorganize the content that is not detailed and inaccurate. The Version 2 was released in November 2018. The Threat Framework Version 2 consists of 6 stages, 21 objectives, 188 actions, and several key phrases. It provides a standard definition that guides the attacker’s life cycle. The activities show the whole picture of the attack, visualize the strategies and means used by the attackers, and assist the security personnel to develop targeted defense measures.
Because the Threat Framework attempts to cover a wide range of possible goals and behaviors, it also includes its own and associated proprietary attack capabilities. For example, the “Equation Group”covers the ability to persist firmware of various models of hard drives, the ability of the QUANTUM attack system to modify the communication path, and the ability of the passive signal collection system (TURMOIL) under the “turbulent flow” framework to send beacons and counterfeit legal traffic to the midpoints. Therefore, the “threat framework” has become a very effective method framework for sorting out cyber attacks from ultra-high-capacity cyber threat actors.
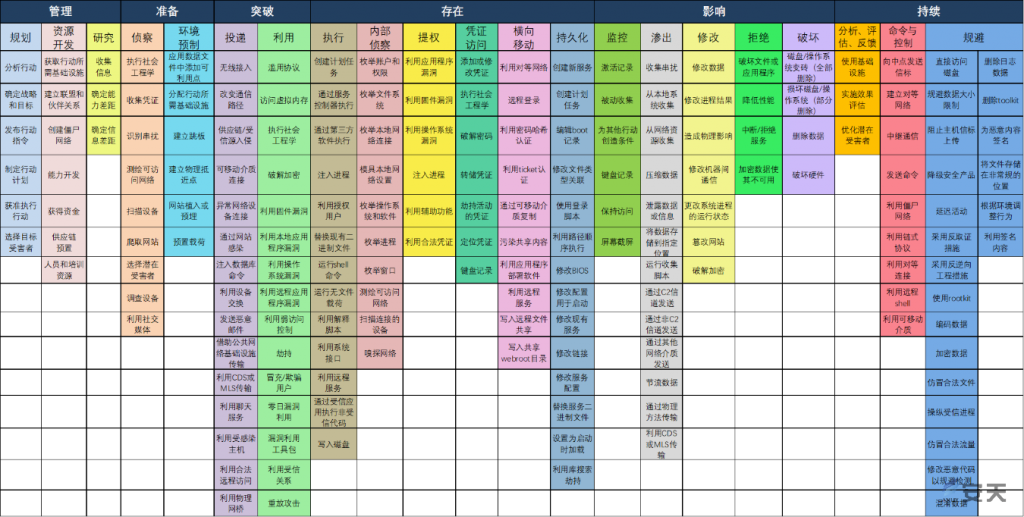
Figure 5-1 NSA/CSS Technical Cyber Threat Framework
Taking “Threat Framework” V2 as the reference, Antiy has described and classified the behaviors at each stage of the attack activities launched by cyber threat actors with ultra high capability, assisted in analyzing the intentions and behaviors of these actors, and provided reference for the implementation of relevant defensive work.
Through the re-analysis of this event, the threat behaviors involved in this event can be mapped to the “Threat Framework” V2. Based on the long-term environmental preparation, attackers set up a large number of jumpserver resources in multiple countries or regions and can launch attacks at any time. Attackers use ZESTYLEAK, BARGLEE, and BANANAGLEE attack equipment to attack firewalls, obtain firewall permissions, and realize the control of the devices and the management of the servers. After obtaining the control of the servers by using the “Eternal” series vulnerabilities, attackers can execute the sql scripts, query the information in the Oracle database connected to the servers, and obtain credentials and internal architecture information. Using the acquired credentials to remotely log in to the relevant Windows hosts and servers, attackers can continue to collect relevant user credentials by moving laterally to hosts in different office locations. Finally, evasion methods such as data encryption can be used to prevent victims from detecting threats. These activities can be mapped to the categories and actions of the “Threat Framework”.
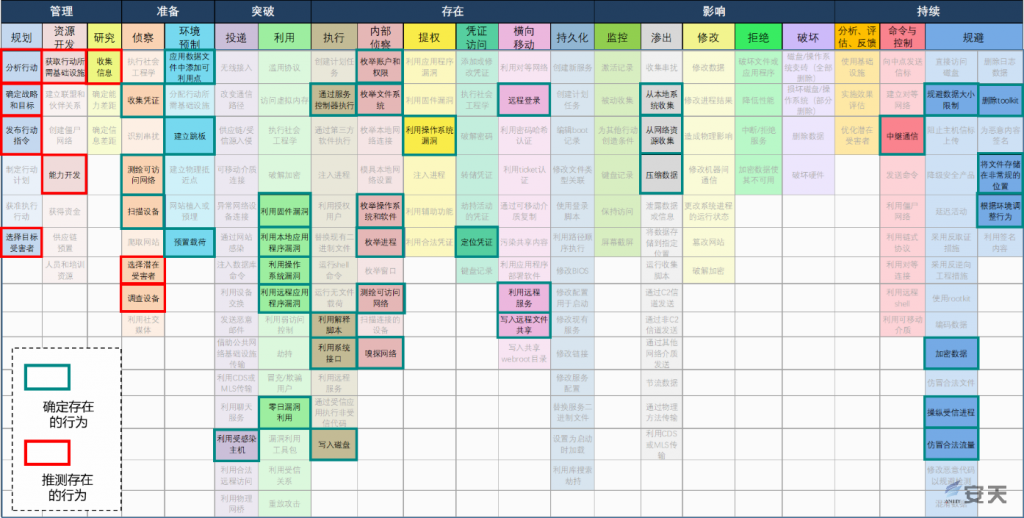
Figure 5-2 This event maps to the “Threat Framework”
This event involved a total of 47 behaviors from 15 targets, including both speculative and definitive behaviors. After analysis, the behaviors determined to use are as follows:
- Reconnaissance: collect credentials, map accessible networks, scan devices;
- Staging: add available points to application data files, create midpoints, preset payload;
- Delivery: use compromised host;
- Exploitation: exploit firmware vulnerability, exploit local application vulnerability, exploit OS vulnerability, exploit remote application vulnerability, exploit zero-day vulnerability;
- Execution: execute via service controller, use interpreted scripts, use system interface, write to disk;
- Internal reconnaissance: enumerate accounts and permissions, enumerate file system, enumerate OS and software, enumerate processes, map accessible networks, sniff network;
- Privilege escalation: exploit OS vulnerability;
- Credential access: locate credentials;
- Lateral movement: logon remotely, use remote services, write to remote file shares;
- Exfiltrate: collect from local system, collect from network resources, compress data;
- Command and Control: relay communications;
- Evasion: avoid data-size limits, encrypt data, manipulate trusted process, mimic legitimate traffic, employ rootkits, store files in unconventional location, tailor behavior to environment.
At the same time, there must be systematic prophase preparatory work for such complex, rigorous attacks that employ a large number of cyber attack equipment resources, including planning, identifying targets, selecting attack equipment (may also include temporary development of equipment for IT scenarios not covered by existing attack equipment) , etc.
6 .Event summary
Based on the re-analysis of the compromised assets, the attack equipment used and the attack process, this report basically presents the overall picture of the attack. From the background of the event (2012~2013) , the deployment and defense situation of the compromised targets generally reflects the deployment and defense characteristics for information assets in that era. The deployment includes VPN, firewall, host antivirus and other basic security parts, basic partitioning of internal assets, and the certain configuration reinforcement, etc. These protection methods are the basic work for establishing network defense systems, which is effective for preventing common network attacks. However, it is completely insufficient to prevent cyber threat actors with ultra high capability.
In the meantime, relevant leaked information shows that the system administrators has some very obvious configuration and security policy errors. For example, multiple servers in the same group use the same supervisor password, so that once one of the password has been extracted, restored or sniffed, all can be broken through; the passwords of servers in different groups have obvious predictable “common part + serial number” rules; the firewall does not have a specific restriction policy for IP addresses that can access the management interface, etc.
The establishment of a defense system that can effectively defend against advanced cyber threat actors is not a simple process to fill in gaps, but a complex and arduous process:
- It is necessary to confront the security challenges brought by the growth of open scenarios and information systems, comprehensively improve network security planning capabilities, and implement security planning, construction, operation and maintenance throughout the whole life cycle. The era of traditional banking systems relying on physical security isolation to protect their assets has long passed. With the advent of inter-bank transfer, deposit and withdrawal, services like SWIFT, they have to become the infrastructure that can be accessible on the public network. We must be based on the realistic conditions of open scenarios and the premise of the increasing scale and complexity of information systems. The larger the openness and scale of information systems, the more we need to synchronously improve the overall network security ability in the planning, construction and operation and maintenance throughout the whole life cycle, and implement the comprehensive security planning of the system.
- Important and large-scale information assets need to set “the enemy is inside, the enemy will be inside” as the objective enemy situation setting. In view of the scale of information systems, the complexity of the supply chains, and the inevitability of various information exchange, it is a highly unrealistic imagination to block threats outside the border (security gateway or GAP). For the super cyber threat actors who have a large number of equipments to break through the isolated network , penetrate the distribution logistics parts, and can carry out the upstream supply chain preset operations, they may break through the network border layer by layer, or directly build internal bridgehead with the help of other operations. Therefore, for critical infrastructure and important information systems, “the enemy is inside, the enemy will be inside” must be set as the most basic enemy situation setting. In 2017, Antiy put forward the view that “effective enemy situation is the premise of doing a good job in network security defense” , which is a defensive thinking derived from military exercises. However, practices are constantly driven by the concept in the last two years, we feel that the risks in cyberspace are more serious than the exercise supposed. “The enemy will be inside” can be regarded as an assumption to guide the planning that can nip in the bud. However, “the enemy is inside” has already formed a “real war situation” and needs the threat hunting ability to “find out and drive out” the threat actors.
- Refer to the “Threat Framework”, we can update the systematic cognition of threat actors and attack activities to deepen and perfect the enemy situation setting and improve defense. Cyber defenders must confront advanced cyber threat actors who have a large number of advanced equipment and attack resources. Their actions are a combination of complex processes. Complex processes are not necessarily supported by “advanced” attack means and equipment. On the one hand, some low-level configuration errors and unpatched vulnerabilities can become the entry point for threat actors; on the other hand, advanced cyber threat actors can also hijack and use botnets or other resources controlled by low-level cyber threat actors. Treating security defense work as the response to various threat types such as malicious code, DDoS, website defacement, botnets and so on, and stacking products obviously cannot integrate the effective defense system. Starting from the threat framework and deducing each stage and behavior of the threats is beneficial to not only evaluate the effectiveness and rationality of the current defense system and related security product capabilities, but also form systematic defense planning and construction objectives.
- Any single point may be compromised or disabled, including the network security itself. In the process of the re-analysis, we can find that although the whole SWIFT system uses two-tiered firewall for defense, attackers have developed adaptive attack equipment for all major IT device scenarios, including various popular firewalls. So any single point may be compromised or disabled, including the network security itself. Firewall is a requisite network security device. For example, it is an effective way to equip full-flow monitoring and recording device such as Antiy Persistent Threat Detection System for important border security device, and then transferring the data results to the inside through uni-directional GAP for the situational awareness platform to conduct in-depth analysis. It can not only make up for the deficiency of detection depth caused by the efficiency request of firewall devices and further enhance the border defense capability, but also can record and retain the attack traffic of the firewall, and provide the necessary basis for the subsequent threat discovery, forensics, traceability, hunting, etc.
- Comprehensive and accurate detection and protection capabilities for known threats and discovery capabilities for unknown threats are both very important. Under the enemy situation setting, we can find that the attack equipment used by advanced cyber threat actors is likely to be “unknown”. This unknown means that under local or global conditions, the attack equipment is an unacquired or at least unrecognized threat to defenders and their supporting strength (such as network security vendors). However, if we cannot effectively defend against the known threats, it will be more difficult to defend against the threat actors with ultra high capability. We notice that similar vulnerability exploitation tools used to attack EastNets have become “known threats” after being revealed by the analysis report, and have been widely used by lower-level attackers to make larger impact and damage. Effective defense for these threats is a necessary basic capability. For unknown threats, it is impossible to prevent them breaking through the defense for the first time, therefore, a rational defense system should be used to control the scope of their activities and limit their ability to move laterally. Since unknown threats may cause original detection capability to fail to leave a trace of attackers, a more comprehensive data collection capability and defense in depth based on the failure design are required. At the same time, in the process of confrontation with threats, it is also an indispensable capability to be able to accurately detect massive known threat events.
- Establish “systematic defense” to deal with “systematic attacks”. In the case of systematic attacks by advanced cyber threat actors, only single-point or simple multi-point protection is not enough to form an effective defense system. The single-point confrontation must be transformed into systemic confrontation, and the simple product pile-up must be transformed into an organic integration of capabilities. On the basis of the “sliding scale” model [16] proposed by the international network security research institute SANS, Antiy has extended the basic model with a number of Chinese manufacturers, and proposed the cyberspace security overlay evolution model. This model divides cybersecurity capabilities into five major areas. Among them, infrastructure security, defense in depth, situational awareness and active defense, and threat intelligence are all necessary for a complete network security defense system. The technical hierarchy of the physical environment, the communication network, the computing environment, the application, and the data in which the protected target is located is effectively associated with the model, and the required security measures can be quickly found. On the basis of manageability and security, combined with reasonable defense in depth, situational awareness and active defense can play a corresponding role to coordinate the deployment of security products. The value of threat intelligence can be maximized. Against advanced cyber threat actors, system construction and investment must be carried out in terms of situational awareness, active defense and threat intelligence, but at the same time the effectiveness of such input depends on the support of infrastructure security and defense in depth. It is necessary to see that situational awareness, active defense and threat intelligence require high investment, which is consistent with the fact that security confrontation is both systemic confrontation and cost confrontation.
- Situational awareness must combine with tactical responses in order to cope with the high-speed and variability of cyberspace threats. We can’t stay in the “control” and strategic adjustment of “macro situation”, since the information security life-cycle based on PDCA cycle can’t resist attacks that happen fast. The attack equipment and related technical actions of such attacks are highly concealed, which will not trigger the alarms of firewall, intrusion detection and host antivirus software, nor will it bring obvious traffic anomalies and mutations. Lateral movement, control, and stealing operations are intermingled with normal system traffic. Timely discovery of such micro-details, rapid detection, understanding, decision-making and execution, thus achieving the goal of resisting attacks, recovering and even implementing counter-attacks, are the goals of active defense (see Cyber Defense and Situational Awareness translated by Antiy and industry experts and the translator’s preface [17]). This situational awareness system is not a simple macro-level monitoring + large screen, but a complex tactical situational awareness platform system, which is an important strategic direction that Antiy is making full efforts.
- To ensure the security of important information assets and large-scale information assets, a practical operational mechanism must be established. “Systematic defense” is not just systematic deployment of security products. “Situational awareness” is not just situational awareness of machines. To play the role of the system, it is necessary to establish a complete security operation process, implement the relevant roles and responsibilities of the security operation, and formulate and improve the supporting security operation specification process. Although most of the security measures deployed in infrastructure security and defense in depth are effective without human involvement, they also require updates, maintenance and audit. The timely and continuous work is the basis in ensuring the effectiveness of security measures. It is necessary to establish the basic security operation and maintenance capability of “asset, configuration, patch, vulnerabilities, and operation and maintenance security integration”. Situational awareness and active defense are designed around the cyberspace defense personnel, and they are more dependent on the practical operational mechanism, so that “people on the loop” can play a key role. The security products, systems and platforms provided by future security vendors must meet the requirements of the overall requirements of the practical operation.
- Finally, and most importantly, the ultra-high-capacity cyber threat actors are not unstoppable. It is necessary to have full understanding of the capability of the ultra-high-capacity cyber threat actors, and to avoid demonization of them and the nihilism of defense. Take Equation Group as an example, the group demonstrated the ultra-attack capability in the “JEEPFLEA_MARKET” operation, but in another attack on EastNets partner BCG in Latin America and the Caribbean, the group was unsuccessful. For advanced cyber threats, from defense to hunting, we can’t hope for good luck, nor threat actors’ give-up. We need to establish firm belief, overcome the gap between the defensive capabilities needed to deal with the enemy, and be prepared for the long-term, sustained and solid foundation work.
There’s still a long way to go. I’ll be indomitable, spare no pains to seek and explore.
But one thing that can be determined is that, we start today and we will reach the goal one day earlier than we start tomorrow.
Postscript of the analysis team
This report has undergone many revisions and improvements. In the process of recurrence analysis, we are under huge pressure, anxiety and responsibility. In front of the attack capability that the ultra-high-capacity cyber threat actors have already possessed in 2012~2013, it is very difficult to establish the corresponding defensive capability, but it is a goal that must be achieved. At the same time, we are also very worried about them unrestrainedly improving attack capability, which will make the cyberspace weaponization a turbulent countercurrent.
The release date of the report is the International Children’s Day on June 1st. There is such a call in the World Children’s Peace Treaty:
We, children of the world, declare that the future world should be peaceful.
We want a planet without war and weapons…
Appendix 1: Threat levels of cyberspace threat actors classified by Antiy
| Threat Level | Defense Target | Characteristics | Attack Technologies and Tools |
| 0 | Amateur hackers | Public attack technologies and tools | |
| 1 | Level 0 target + black industry groups | Non-state actors, driven by financial interests | Public attack technologies, tools and platforms; some proprietary attack technologies, tools and platforms |
| 2 | Level 1 target + cybercrime gangs or hacker groups | Non-state actors, driven by financial interests, may also be driven by ideology, and dare cause greater damage or influence. | Proprietary attack technologies, tools and platforms; vulnerability mining and utilization technology development capabilities |
| 3 | Level 2 target + cyber terrorist groups | Non-state actors, driven by ideology, seeking to maximize damages or impacts | Proprietary attack technologies, tools and platforms; vulnerability mining and utilization technology development capabilities |
| 4 | Level 3 target + general capability state/regional actor | state/regional actors, driven by state/regional interests, cyber espionage and cyber warfare integration, seeking to gain political, economic and military advantages through cyber warfare | Partial control over the its own state/regional network infrastructure; proprietary attack technologies, tools and platforms; vulnerability mining and utilization technology development capabilities; mastering a small number of 0day vulnerabilities |
| 5 | Level 4 target + advanced capability state/regional actor | state/regional actors, driven by state/regional interests, cyber espionage and cyber warfare integration, seeking to gain political, economic and military advantages through cyber warfare | Partial control over the its own state/regional network infrastructure; proprietary attack technologies, tools and platforms; vulnerability mining and utilization technology development capabilities; Multiple 0day vulnerabilities |
| 6 | Level 5 target + ultra-high-capacity state/regional actor | state/regional actors, driven by state/regional interests, cyber espionage and cyber warfare integration, seeking to gain political, economic and military advantages through cyber warfare | Control over your state/regional network infrastructure, external state/regional network infrastructure, Internet-level network infrastructure, and partial control over information technology supply chain; proprietary attack technologies, tools and platforms; highly integrated across-dimension attack means; vulnerability mining and utilization technology development capabilities; vulnerability manufacturing capabilities; mastering a large number of 0day vulnerabilities |
Appendix 2: References
- [Kaspersky:Equation: The Death Star of Malware Galaxy]
http://securelist.com/blog/research/68750/equation-the-death-star-of-malware-galaxy/
- [安天:修改硬盘固件的木马——探索方程式(EQUATION)组织的攻击组件]
https://www.antiy.com/response/EQUATION_ANTIY_REPORT.html
- [安天:方程式(EQUATION)部分组件中的加密技巧分析]
- [安天:从“方程式”到“方程组”EQUATION攻击组织高级恶意代码的全平台能力解析]
https://www.antiy.com/response/EQUATIONS/EQUATIONS.html
- [安天:方程式组织EQUATION DRUG平台解析——方程式组织系列分析报告之四]
https://www.antiy.com/response/EQUATION_DRUG/EQUATION_DRUG.html
- [安天:对Stuxnet蠕虫攻击工业控制系统事件的综合分析报告]
https://www.antiy.com/response/stuxnet/Report_on_the_Worm_Stuxnet_Attack.html
- [安天:Flame蠕虫样本集分析报告]
https://www.antiy.com/response/flame/Analysis_on_the_Flame.html
- [安天:探索Duqu木马的身世之谜——Duqu和Stuxnet同源性分析]
http://www.antiy.com/cn/security/2012/r120521_001.htm
- [EastNets]
https://www.eastnets.com/about
- [How to Pick a SWIFT Service Bureau]
https://www.treasuryandrisk.com/2010/10/01/how-to-pick-a-swift-service-bureau/
- [安天:安天关于系统化应对NSA网络军火装备的操作手册]
https://www.antiy.com/response/Antiy_Wannacry_NSA.html
- [Schneier on Security:FEEDTROUGH: NSA Exploit of the Day]
https://www.schneier.com/blog/archives/2014/01/feedtrough_nsa.html
- [美国网络空间攻击与主动防御能力解析(概述篇)]
- [美国用于漏洞利用的网空攻击装备解析]
- [美国用于命令与控制的网空攻击装备解析]
- 国际网络安全研究机构SANS所提出的“滑动标尺”模型
https://www.sans.org/reading-room/whitepapers/analyst/sliding-scale-cyber-security-36240
- [美]亚历山大·科特、克利夫·王、罗伯特·F.厄巴彻编著 黄晟 安天研究院译. 网络空间安全防御与态势感知[M]北京:机械工业出版社,2019.
